What should you do first?
You have an Azure subscription that contains an Azure Active Directory (Azure AD) tenant named contoso.com and an Azure Kubernetes Service (AKS) cluster named AKS1.
An administrator reports that she is unable to grant access to AKS1 to the users in contoso.com.
You need to ensure that access to AKS1 can be granted to the contoso.com users.
What should you do first?
A . From contoso.com, modify the Organization relationships settings.
B . From contoso.com, create an OAuth 2.0 authorization endpoint.
C . Recreate AKS1.
D . From AKS1, create a namespace.
Answer: B
Explanation:
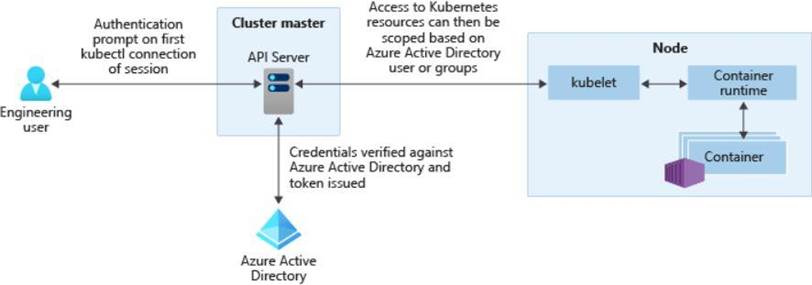
With Azure AD-integrated AKS clusters, you can grant users or groups access to Kubernetes resources within a namespace or across the cluster. To obtain a kubectl configuration context, a user can run the az aks get-credentials command. When a user then interacts with the AKS cluster with kubectl, they’re prompted to sign in with their Azure AD credentials. This approach provides a single source for user account management and password credentials. The user can only access the resources as defined by the cluster administrator.
Azure AD authentication is provided to AKS clusters with OpenID Connect. OpenID Connect is an identity layer built on top of the OAuth 2.0 protocol. For more information on OpenID Connect, see the Open ID connect documentation. From inside of the Kubernetes cluster, Webhook Token Authentication is used to verify authentication tokens. Webhook token authentication is configured and managed as part of the AKS cluster.
Reference:
https://kubernetes.io/docs/reference/access-authn-authz/authentication/
https://docs.microsoft.com/en-us/azure/aks/concepts-identity
Latest AZ-104 Dumps Valid Version with 416 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

