Which three actions should you perform in sequence?
Topic 7, Contoso, Ltd Case D
Overview
Contoso, Ltd., is a manufacturing company that makes several different components that are used in automobile production. Contoso has a main office in Detroit, a distribution center in Chicago, and branch offices in Dallas, Atlanta, and San Diego.
The contoso.com forest and domain functional level are Windows Server 2008 R2. All servers run Windows Server 2012 R2, and all client workstations run Windows 7 or Windows 8. Contoso uses System Center 2012 Operations Manager and Audit Collection Services (ACS) to monitor the environment. There is no certification authority (CA) in the environment.
Current Environment
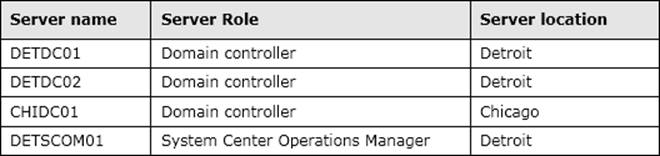
The contoso.com domain contains the servers as shown in the following table:
Contoso sales staff travel within the United States and connect to a VPN by using mobile devices to access the corporate network. Sales users authenticate to the VPN by using their Active Directory usernames and passwords. The VPN solution also supports certification-based authentication.
Contoso uses an inventory system that requires manually counting products and entering that count into a database. Contoso purchases new inventory software that supports wireless handheld scanners and several wireless handheld scanners. The wireless handheld scanners run a third party operating system that supports the Network Device Enrollment Service (NDES).
Business Requirements
Security
The wireless handheld scanners must use certification-based authentication to access the wireless network.
Sales users who use mobile devices must use certification-based authentication to access the VPN. When sales users leave the company, Contoso administrators must be able to disable their VPN access by revoking their certificates.
Monitoring
All servers must be monitored by using System Center 2012 Operating Manager. In addition to monitoring the Windows operating system, you must collect security logs from the CA servers by using ACS, and monitor the services that run on the CA and Certificate Revocation List (CRL) servers, such as certification authority and web services.
Technical Requirements
CA Hierarchy
Contoso requires a two-tier CA hierarchy. The CA hierarchy must include a stand-alone offline root and two Active Directory-integrated issuing CAs: one for issuing certificates to domain-joined devices, and one for issuing certificates to non-domain-joined devices by using the NDES. CRLs must be published to two web servers: one in Detroit and one in Chicago.
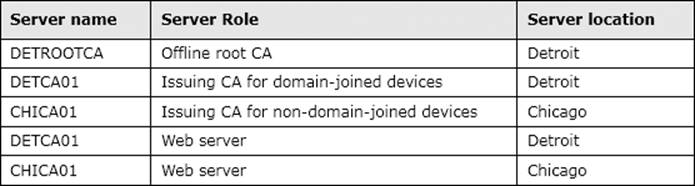
Contoso has servers that run Windows Server 2012 R2 to use for the CA hierarchy. The servers are described in the following table:
The IT security department must have the necessary permissions to manage the CA and CRL servers. A domain group named Corp-IT Security must be used for this purpose. The IT security department users are not domain admins.
Fault Tolerance
The servers that host the CRL must be part of a Windows Network Load Balancing (NLB) cluster. The CRL must be available to users in all locations by using the hostname crl.contoso.com, even if one of the underlying web servers is offline.
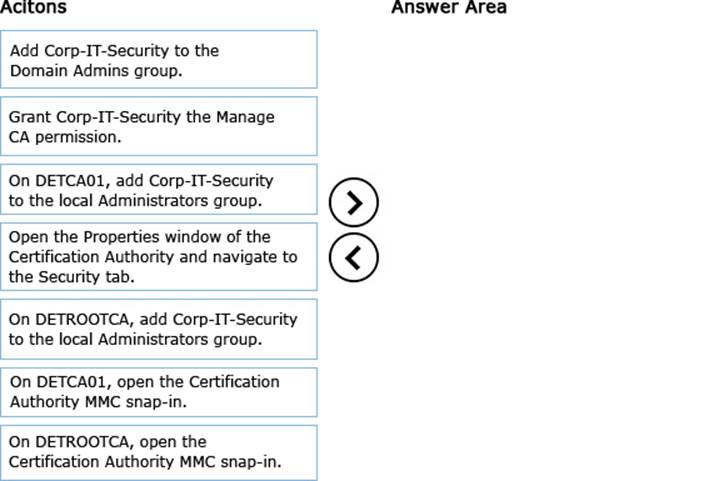
DRAG DROP
You need to delegate permissions for DETCA01.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Answer: 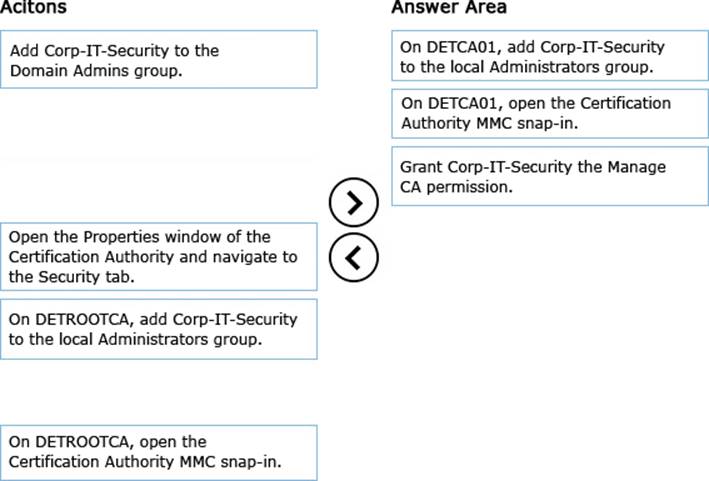
Explanation:
Reference: Implement Role-Based Administration
https://technet.microsoft.com/en-us/library/cc732590.aspx

