Which of the following statements is incorrect?
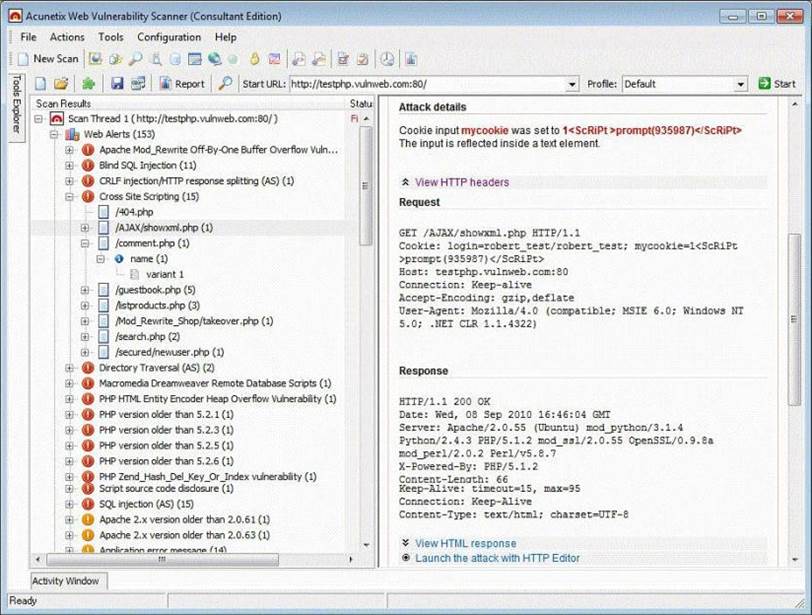
Vulnerability scanners are automated tools that are used to identify vulnerabilities and misconfigurations of hosts. They also provide information regarding mitigating discovered vulnerabilities.
Which of the following statements is incorrect?
A . Vulnerability scanners attempt to identify vulnerabilities in the hosts scanned.
B . Vulnerability scanners can help identify out-of-date software versions, missing patches, or system upgrades
C . They can validate compliance with or deviations from the organization’s security policy
D . Vulnerability scanners can identify weakness and automatically fix and patch the vulnerabilities without user intervention
Answer: D
Latest CEH-001 Dumps Valid Version with 878 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments

