What type of attack is this?
John is investigating web-application firewall logs and observers that someone is attempting to inject the following:
char buff[10];
buff[>o] – ‘a’:
What type of attack is this?
A . CSRF
B . XSS
C . Buffer overflow
D . SQL injection
Answer: C
Explanation:
Buffer overflow this attack is an anomaly that happens when software writing data to a buffer overflows the buffer’s capacity, leading to adjacent memory locations being overwritten. In other words, an excessive amount of information is being passed into a container that doesn’t have enough space, which information finishes up replacing data in adjacent containers. Buffer overflows are often exploited by attackers with a goal of modifying a computer’s memory so as to undermine or take hold of program execution.
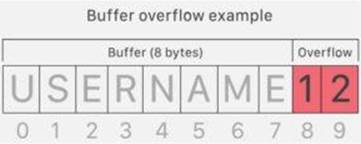
What’s a buffer? A buffer, or data buffer, is a neighborhood of physical memory storage wont to temporarily store data while it’s being moved from one place to a different. These buffers typically sleep in RAM memory. Computers frequently use buffers to assist improve performance; latest hard drives cash in of buffering to efficiently access data, and lots of online services also use buffers. for instance, buffers are frequently utilized in online video streaming to stop interruption. When a video is streamed, the video player downloads and stores perhaps 20% of the video at a time during a buffer then streams from that buffer. This way, minor drops in connection speed or quick service disruptions won’t affect the video stream performance. Buffers are designed to contain specific amounts of knowledge. Unless the program utilizing the buffer has built-in instructions to discard data when an excessive amount of is shipped to the buffer, the program will overwrite data in memory adjacent to the buffer. Buffer overflows are often exploited by attackers to corrupt software. Despite being well-understood, buffer overflow attacks are still a serious security problem that torment cyber-security teams. In 2014 a threat referred to as ‘heartbleed’ exposed many many users to attack due to a buffer overflow vulnerability in SSL software.
How do attackers exploit buffer overflows? An attacker can deliberately feed a carefully crafted input into a program which will cause the program to undertake and store that input during a buffer that isn’t large enough, overwriting portions of memory connected to the buffer space. If the memory layout of the program is well-defined, the attacker can deliberately overwrite areas known to contain executable code. The attacker can then replace this code together with his own executable code, which may drastically change how the program is meant to figure .For example if the overwritten part in memory contains a pointer (an object that points to a different place in memory) the attacker’s code could replace that code with another pointer that points to an exploit payload. this will transfer control of the entire program over to the attacker’s code.
Latest 312-50v11 Dumps Valid Version with 432 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

