What should you do?
Topic 1, Litware, inc
Litware, inc
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other question on this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next sections of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question on this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
Overview
Litware, Inc. is a digital media company that has 500 employees in the Chicago area and 20 employees in the San Francisco area.
Existing Environment
Litware has an Azure subscription named Sub1 that has a subscription ID of 43894a43-17c2-4a39-8cfc-3540c2653ef4.
Sub1 is associated to an Azure Active Directory (Azure AD) tenant named litwareinc.com. The tenant contains the user objects and the device objects of all the Litware employees and their devices. Each user is assigned an Azure AD Premium P2 license. Azure AD Privileged Identity Management (PIM) is activated.
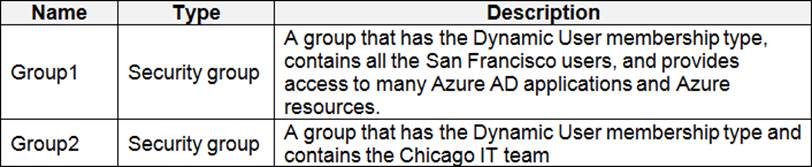
The tenant contains the groups shown in the following table.
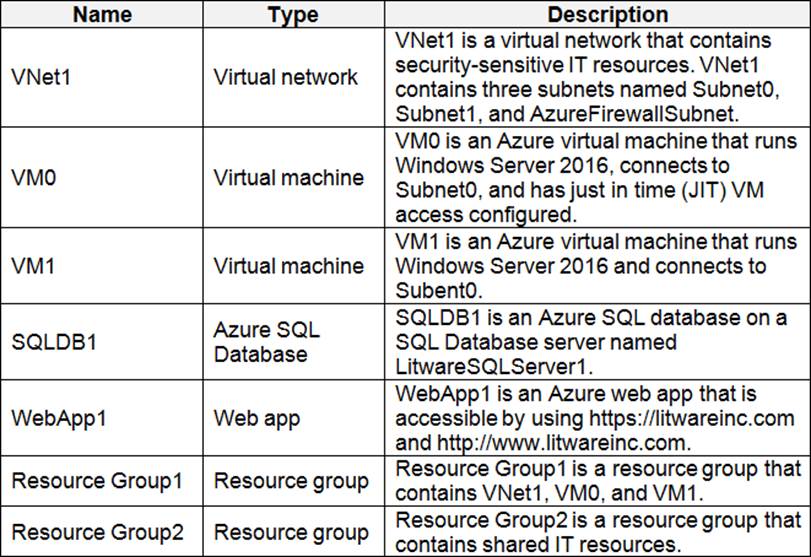
The Azure subscription contains the objects shown in the following table.
Azure Security Center is set to the Free tier.
Requirements
Planned changes
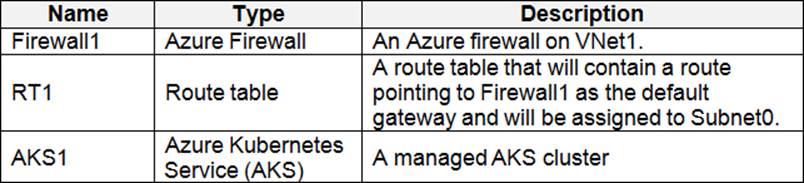
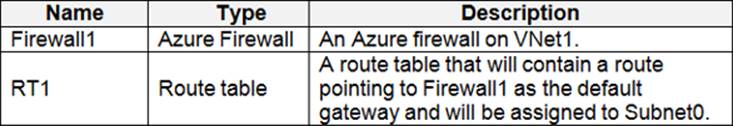
Litware plans to deploy the Azure resources shown in the following table.
Identity and Access Requirements
Litware identifies the following identity and access requirements:
• All San Francisco users and their devices must be members of Group1.
• The members of Group2 must be assigned the Contributor role to Resource Group2 by using a permanent eligible assignment.
• Users must be prevented from registering applications in Azure AD and from consenting to applications that access company information on the users’ behalf.
Platform Protection Requirements
Litware identifies the following platform protection requirements:
• Microsoft Antimalware must be installed on the virtual machines in Resource Group1.
• The members of Group2 must be assigned the Azure Kubernetes Service Cluster Admin Role.
• Azure AD users must be to authenticate to AKS1 by using their Azure AD credentials.
• Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
• A new custom RBAC role named Role1 must be used to delegate the administration of the managed disks in Resource Group1. Role1 must be available only for Resource Group1.
Security Operations Requirements
Litware must be able to customize the operating system security configurations in Azure Security Center.
You need to ensure that users can access VM0. The solution must meet the platform protection requirements.
What should you do?
A . Move VM0 to Subnet1.
B . On Firewall, configure a network traffic filtering rule.
C . Assign RT1 to AzureFirewallSubnet.
D . On Firewall, configure a DNAT rule.
Answer: A
Explanation:
Azure Firewall has the following known issue:
Conflict with Azure Security Center (ASC) Just-in-Time (JIT) feature.
If a virtual machine is accessed using JIT, and is in a subnet with a user-defined route that points to Azure Firewall as a default gateway, ASC JIT doesn’t work. This is a result of asymmetric routing C a packet comes in via the virtual machine public IP (JIT opened the access), but the return path is via the firewall, which drops the packet because there is no established session on the firewall.
Solution: To work around this issue, place the JIT virtual machines on a separate subnet that doesn’t have a user-defined route to the firewall.
Scenario:
Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
References: https://docs.microsoft.com/en-us/azure/firewall/overview
Latest AZ-500 Dumps Valid Version with 278 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

