Which of the following technologies is MOST likely being used to provide access to the third company?
A company wants to extend its help desk availability beyond business hours. The Chief Information Officer (CIO) decides to augment the help desk with a third-party service that will answer calls and provide Tier 1 problem resolution, such as password resets and remote assistance. The security administrator implements the following firewall change:
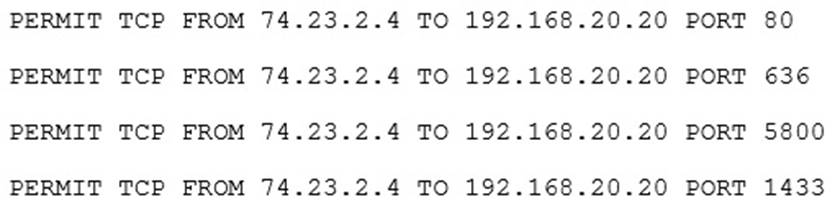
The administrator provides the appropriate path and credentials to the third-party company.
Which of the following technologies is MOST likely being used to provide access to the third company?
A . LDAP
B . WAYF
C . OpenID
D . RADIUS
E . SAML
Answer: D
Latest CAS-003 Dumps Valid Version with 509 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments
Inline Feedbacks
View all comments

