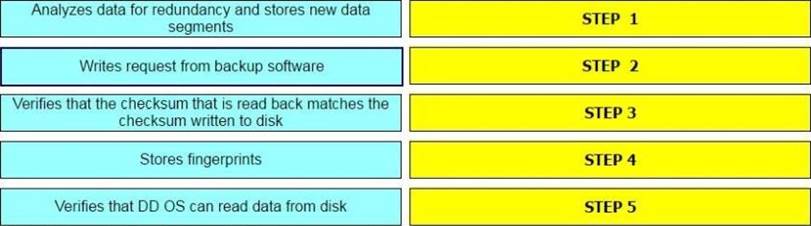
What is the correct sequence of operations used by the Dell EMC Data Domain Data Invulnerability Architecture (DIA) in the end-to-end verification process?
DRAG DROP
What is the correct sequence of operations used by the Dell EMC Data Domain Data Invulnerability Architecture (DIA) in the end-to-end verification process?
Answer: 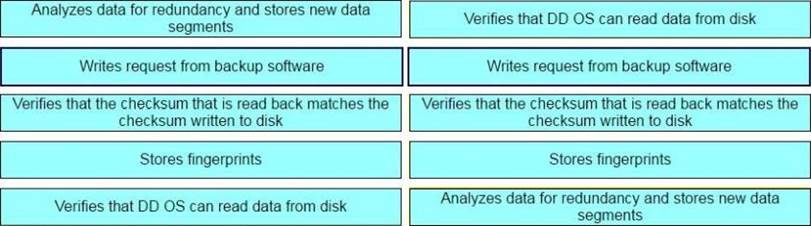
Latest E20-385 Dumps Valid Version with 171 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments

