Paloalto Networks PCCET Palo Alto Networks Certified Cybersecurity Entry-level Technician Online Training
Paloalto Networks PCCET Online Training
The questions for PCCET were last updated at May 13,2024.
- Exam Code: PCCET
- Exam Name: Palo Alto Networks Certified Cybersecurity Entry-level Technician
- Certification Provider: Paloalto Networks
- Latest update: May 13,2024
Which aspect of a SaaS application requires compliance with local organizational security policies?
- A . Types of physical storage media used
- B . Data-at-rest encryption standards
- C . Acceptable use of the SaaS application
- D . Vulnerability scanning and management
In which phase of the cyberattack lifecycle do attackers establish encrypted communication channels back to servers across the internet so that they can modify their attack objectives and methods?
- A . exploitation
- B . actions on the objective
- C . command and control
- D . installation
C
Explanation:
Command and Control: Attackers establish encrypted communication channels back to command-and-control (C2) servers across the internet so that they can modify their attack objectives and methods as additional targets of opportunity are identified within the victim network, or to evade any new security countermeasures that the organization may attempt to deploy if attack artifacts are discovered.
Which Palo Alto subscription service identifies unknown malware, zero-day exploits, and advanced persistent threats (APTs) through static and dynamic analysis in a scalable, virtual environment?
- A . DNS Security
- B . URL Filtering
- C . WildFire
- D . Threat Prevention
C
Explanation:
"The WildFire cloud-based malware analysis environment is a cyber threat prevention service that identifies unknown malware, zero-day exploits, and advanced persistent threats (APTs) through static and dynamic analysis in a scalable, virtual environment. WildFire automatically disseminates updated protections in near-real time to immediately prevent threats from spreading; this occurs without manual intervention"
Which network analysis tool can be used to record packet captures?
- A . Smart IP Scanner
- B . Wireshark
- C . Angry IP Scanner
- D . Netman
Which network firewall primarily filters traffic based on source and destination IP address?
- A . Proxy
- B . Stateful
- C . Stateless
- D . Application
What should a security operations engineer do if they are presented with an encoded string during an incident investigation?
- A . Save it to a new file and run it in a sandbox.
- B . Run it against VirusTotal.
- C . Append it to the investigation notes but do not alter it.
- D . Decode the string and continue the investigation.
Systems that allow for accelerated incident response through the execution of standardized and automated playbooks that work upon inputs from security technology and other data flows are known as what?
- A . XDR
- B . STEP
- C . SOAR
- D . SIEM
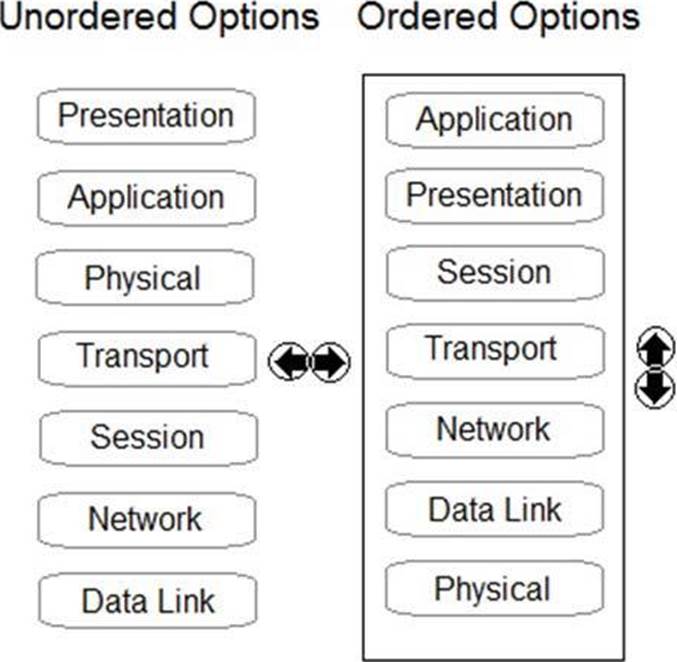
DRAG DROP
Order the OSI model with Layer7 at the top and Layer1 at the bottom.
Which of the following is a Routed Protocol?
- A . Routing Information Protocol (RIP)
- B . Transmission Control Protocol (TCP)
- C . Internet Protocol (IP)
- D . Domain Name Service (DNS)
Which classification of IDS/IPS uses a database of known vulnerabilities and attack profiles to identify intrusion attempts?
- A . Statistical-based
- B . Knowledge-based
- C . Behavior-based
- D . Anomaly-based
B
Explanation:
A knowledge-based system uses a database of known vulnerabilities and attack profiles to identify intrusion attempts. These types of systems have lower false-alarm rates than behavior-based systems but must be continually updated with new attack signatures to be effective.
A behavior-based system uses a baseline of normal network activity to identify unusual patterns or levels of network activity that may be indicative of an intrusion attempt. These types of systems are more adaptive than knowledge-based systems and therefore may be more effective in detecting previously unknown vulnerabilities and attacks, but they have a much higher false-positive rate than knowledge-based systems.
Latest PCCET Dumps Valid Version with 75 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

