Given the above information, which of the following steps should be performed NEXT to secure the system?
A security analyst is reviewing the following log after enabling key-based authentication.
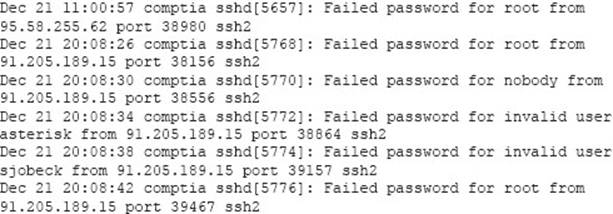
Given the above information, which of the following steps should be performed NEXT to secure the system?
A . Disable anonymous SSH logins.
B . Disable password authentication for SS
D . Disable SSHv1.
E . Disable remote root SSH logins.
Answer: B
Latest CS0-001 Dumps Valid Version with 455 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments
Inline Feedbacks
View all comments

