Cisco 300-206 Implementing Cisco Edge Network Security Solutions Online Training
Cisco 300-206 Online Training
The questions for 300-206 were last updated at Feb 26,2026.
- Exam Code: 300-206
- Exam Name: Implementing Cisco Edge Network Security Solutions
- Certification Provider: Cisco
- Latest update: Feb 26,2026
Which two user privileges does ASDM allow engineer to create? (Choose two)
- A . Full access
- B . admin
- C . read-write
- D . read-only
- E . write-only
Refer to the exhibit.
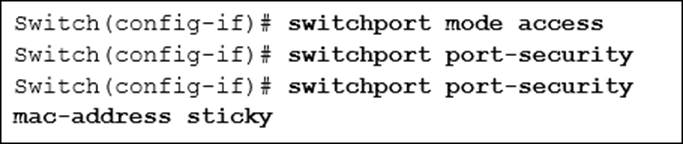
Which two are true statements about the expected port security behavior? (Choose two.)
- A . If a violation occurs, the switch port waits one minute to recover by default.
- B . Only one MAC address can be learned by default on the switch port.
- C . Up to five MAC addresses can be learned by default on the switch port.
- D . If a violation occurs, the switch port remains active, but the traffic is dropped.
- E . If a violation occurs, the switch port shuts down.
An engineer is applying best practices to stop STP unauthorized changes from the uses port.
Which two actions help accomplish this task? (Choose two)
- A . Enable STP Guard
- B . Configure RSTP
- C . Disable STP
- D . Enable BPDU Guard
- E . Enable Root Guard
When you enable IP source Guard on private VLAN ports, which additional action must you take for IP Source Guard to be effective?
- A . Enable DHCP snooping on the isolated VLAN
- B . Enable BPDU guard on the isolated VLAN.
- C . Enable BPDU guard on the primary VLAN.
- D . Enable DHCP snooping on the primary VLAN.
A network engineer wants to add new view to an IOS device configured with RBAC.
Which privilege is required for that task?
- A . Level 16
- B . Level 15
- C . root view
- D . admin view
Refer to the exhibit.
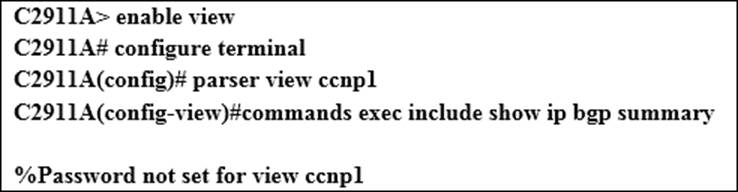
An engineer is configuring IOS role based CLI access and is getting an error upon entering the commands exec include show ip bgp summary parser view command.
Based on the console message received, which command would fix this error?
- A . enable secret <password>
- B . username <user> secret <password>
- C . password <password>
- D . secret 5 <encrypted password>
After a session has been secured with MACsec, which two types of traffic can be sent and received unencrypted?
- A . EAPOL-Start
- B . DHCP offer
- C . Cisco Discovery Protocol
- D . DHCP discover
- E . EAPOL-Logoff
Which two main functions for application inspection on ASA are true?
- A . When services use dynamically assigned ports, the application inspection identifies dynamic port and permits data on these ports.
- B . When services embed IP addresses in the packet, the application inspection translates embedded addresses and updates the checksum.
- C . When services are operating on nonstandard ports, the application inspection identifies the nonstandard port and allows the service to run normally.
- D . When services need IP options to function, the application inspection keeps IP options during the packet transition through the appliance.
- E . When services use load balancing, the application inspection ensures that connections are load blanaced across the servers equally.
An engineer suspects that client workstations are experiencing extremely poor response time due to a man in middle attack.
Which feature must be enabled and configured to provide relief from this type of attack?
- A . Internet Key Exchange
- B . Link Aggregation
- C . Reverse ARP
- D . Dynamic ARP Inspection
- E . private VLANs
Refer to the exhibit.
![]()
Which option describes the role of the filter rule on this cisco ASA firewall?
- A . to discard http traffic destined to a proxy server
- B . to define allowed traffic when the URL filtering server is unavailable
- C . to perform deep packet inspection on all http traffic crossing the Cisco ASA
- D . to send http traffic to a defined URL filtering server
Latest 300-206 Dumps Valid Version with 376 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

