What are two basic rules Check Point recommends for building an effective policy?
What are two basic rules Check Point recommends for building an effective policy?
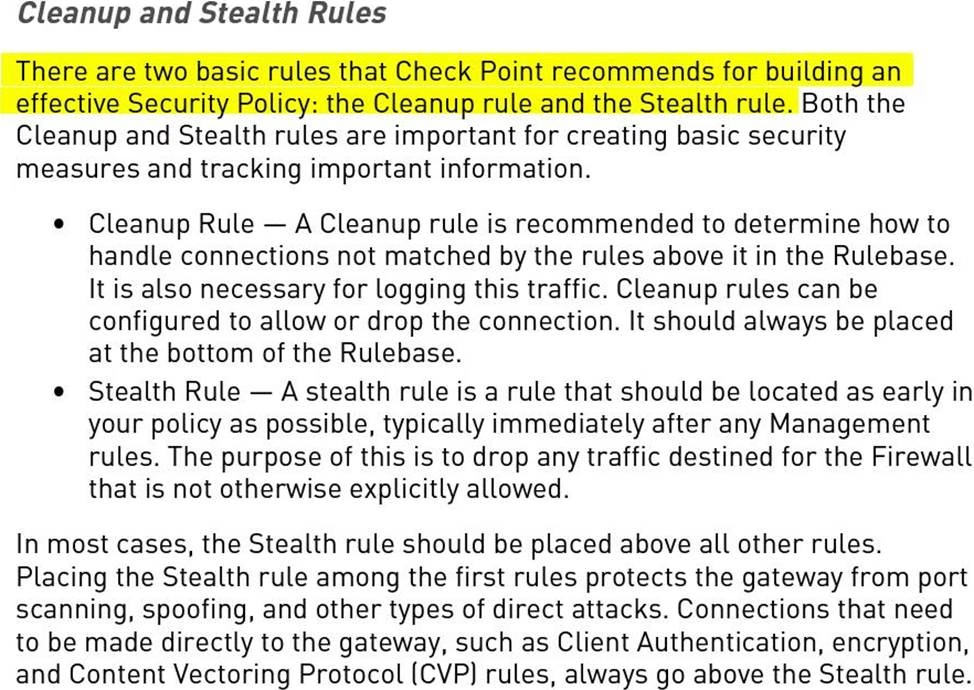
A . Cleanup and Stealth Rule
B . VPN and Admin Rules
C . Implicit and Explicit Rules
D . Access and Identity Rules
Answer: A
Explanation:
Text
Description automatically generated
Latest 156-561 Dumps Valid Version with 83 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments
Inline Feedbacks
View all comments

