Huawei H12-722-ENU HCIP-Security-CSSN(Huawei Certified ICT Professional -Constructing Service Security Network) Online Training
Huawei H12-722-ENU Online Training
The questions for H12-722-ENU were last updated at Jun 01,2026.
- Exam Code: H12-722-ENU
- Exam Name: HCIP-Security-CSSN(Huawei Certified ICT Professional -Constructing Service Security Network)
- Certification Provider: Huawei
- Latest update: Jun 01,2026
If the user’s FTP operation matches the FTP filtering policy, which actions can be performed? (Multiple choice)
- A . Blocking
- B . Announcement
- C . Alerts
- D . Execution
About firewalls and IDS, which of the following is true?
- A . Firewall is a bypass device for fine-grained detection
- B . IDS is a straight-path device and can’t perform depth detection
- C . Firewall is unable to detect insider malicious operation or misoperation
- D . IDS can’t interact with the firewall
Which of the following attack types is DDoS attack?
- A . Single package attack
- B . Traffic attack
- C . Malformed packet attack
- D . Snooping scanning attack
Why APT attacks are difficult to defend? Part of the reason is that they use zero-day loopholes to attack. This zero-day loopholes usually takes a lot of time to research and analyze and make corresponding defense methods.
- A . True
- B . False
The following figure shows the configuration of the URL filtering configuration file. Which of the following statements is true about this configuration?
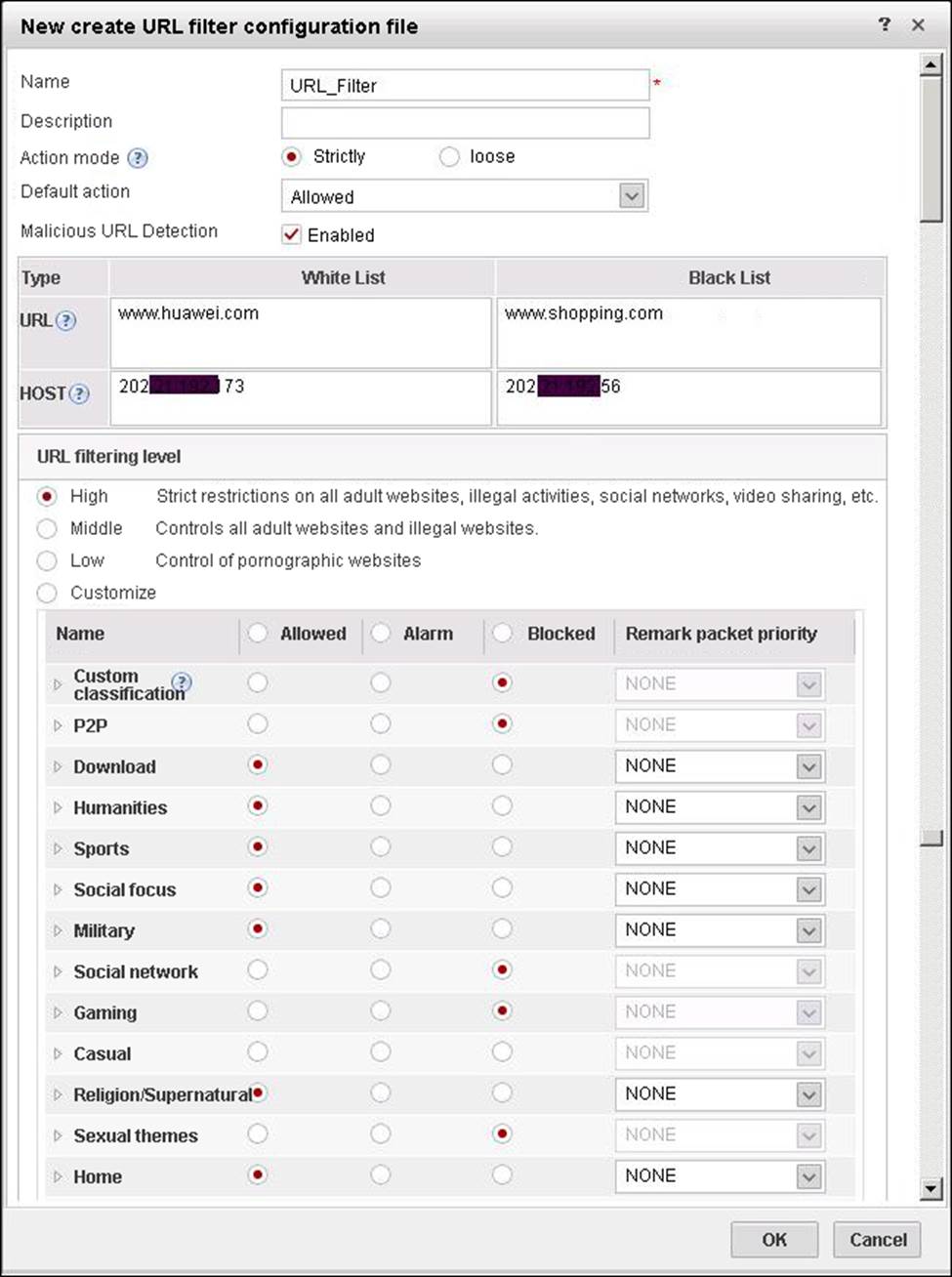
- A . The firewall will check the blacklist first and then check the whitelist.
- B . Assume that user visit www.exzample.com, which is part of Humanities and Social Networking category. At this time, the user cannot access the site.
- C . The user visit the website www.exzample.com. When there is no black and white list of hits, the predefined URL category entry is next queried.
- D . The default action means that all websites allow access. Therefore, this configuration error.
The whitelist rule of the firewall antivirus module is configured as *example*. Which of the following matches is used in this configuration?
- A . Prefix matching
- B . Suffix matching
- C . Keyword matching
- D . exact match
UDP is a connectionless protocol. A large number of UDP flood attacks cause the performance of network devices that rely on session forwarding to be degraded and even the session table is exhausted, causing network congestion.
Which of the following options does not prevent UDP flood attacks?
- A . UDP fingerprint learning
- B . Associated defense
- C . Current limiting
- D . First packet discarded
Regarding the process of file filtering, which of the following statements is wrong?
- A . After the file extraction fails, the file will still be filtered.
- B . The application identification module can identify the type of application hosting the file.
- C . Protocol decoding is responsible for parsing the file data and file transfer directions in the data stream.
- D . The file type identification module is responsible for identifying the real type of the file and the extension of the file based on the file data
Huawei WAF products mainly consist of implementing front-end, back-end central systems and databases. The database mainly stores the front-end detection rules and black and white list configuration files.
- A . True
- B . False
Misuse detection discovers intrusion activity in system by detecting similar behaviors of user intrusions, or by detecting violations of system security rules indirectly by exploiting system flaws.
Which of the following is not misuse detection feature?
- A . Easy to implement
- B . Accurate detection
- C . Effective detection of impersonation of legitimate users
- D . Easy to upgrade

