Docker DCA Docker Certified Associate (DCA) Exam Online Training
Docker DCA Online Training
The questions for DCA were last updated at Jun 01,2026.
- Exam Code: DCA
- Exam Name: Docker Certified Associate (DCA) Exam
- Certification Provider: Docker
- Latest update: Jun 01,2026
Is this a supported user authentication method for Universal Control Plane?
Solution: PAM
- A . Yes
- B . No
Will this sequence of steps completely delete an image from disk in the Docker Trusted Registry? Solution: Delete the image and delete the image repository from Docker Trusted Registry
- A . Yes
- B . No
Will this sequence of steps completely delete an image from disk in the Docker Trusted Registry? Solution: Delete the image and run garbage collection on the Docker Trusted Registry.
- A . Yes
- B . No
Is this the purpose of Docker Content Trust?
Solution: Enable mutual TLS between the Docker client and server.
- A . Yes
- B . No
Is this the purpose of Docker Content Trust?
Solution: Verify and encrypt Docker registry TLS.
- A . Yes
- B . No
Is this a Linux kernel namespace that is disabled by default and must be enabled at Docker engine runtime to be used?
Solution: mnt
- A . Yes
- B . No
Is this a Linux kernel namespace that is disabled by default and must be enabled at Docker engine runtime to be used?
Solution: net
- A . Yes
- B . No
Is this a Linux kernel namespace that is disabled by default and must be enabled at Docker engine runtime to be used?
Solution: user
- A . Yes
- B . No
Is this a way to configure the Docker engine to use a registry without a trusted TLS certificate?
Solution: Pass the ‘–insecure-registry’ flag to the daemon at run time.
- A . Yes
- B . No
The Kubernetes yaml shown below describes a networkPolicy.
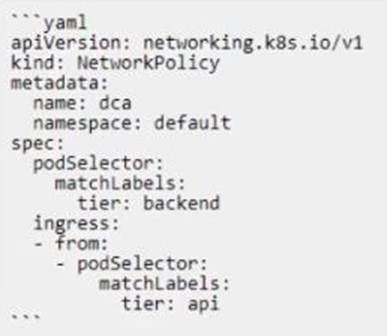
Will the networkPolicy BLOCK this traffic?
Solution: a request issued from a pod bearing the tier: backend label, to a pod bearing the tier:
frontend label
- A . Yes
- B . No
Latest DCA Dumps Valid Version with 55 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

