CompTIA 220-1102 CompTIA A+ Certification Core 2 Exam Online Training
CompTIA 220-1102 Online Training
The questions for 220-1102 were last updated at May 01,2024.
- Exam Code: 220-1102
- Exam Name: CompTIA A+ Certification Core 2 Exam
- Certification Provider: CompTIA
- Latest update: May 01,2024
A technician has verified that a user’s computer has a virus, and the antivirus software is out Of date.
Which of the following steps should the technician take NEXT?
- A . Quarantine the computer.
- B . use a previous restore point,
- C . Educate the end user about viruses
- D . Download the latest virus definitions
A
Explanation:
Quarantining the computer should be the next step because it prevents the virus from spreading to other systems in the network. This can help to contain the infection while further actions are taken to remove the virus. After quarantining the computer, the technician can proceed with steps such as updating the antivirus software, scanning the system, and removing any detected threats.
Which of the following is used as a password manager in the macOS?
- A . Terminal
- B . FileVault
- C . Privacy
- D . Keychain
D
Explanation:
Keychain is a feature of macOS that securely stores passwords, account numbers, and other confidential information for your Mac, apps, servers, and websites1. You can use the Keychain Access app on your Mac to view and manage your keychains and the items stored in them1. Keychain can also sync your passwords and other secure information across your devices using iCloud Keychain1. Keychain can be used as a password manager in macOS to help you keep track of and protect your passwords.
References: 1: Manage passwords using keychains on Mac (https://support.apple.com/guide/mac-help/use-keychains-to-store-passwords-mchlf375f392/mac)
A user received the following error upon visiting a banking website:
The security presented by website was issued a different website’ s address.
A technician should instruct the user to:
- A . clear the browser cache and contact the bank.
- B . close out of the site and contact the bank.
- C . continue to the site and contact the bank.
- D . update the browser and contact the bank.
B
Explanation:
A Windows user recently replaced a computer The user can access the public internet on the computer; however, an internal site at https7/companyintranet.com:8888 is no longer loading.
Which of the following should a technician adjust to resolve the issue?
- A . Default gateway settings
- B . DHCP settings
- C . IP address settings
- D . Firewall settings
- E . Antivirus settings
D
Explanation:
The technician should adjust the firewall settings to resolve the issue of not being able to access an internal site at https://companyintranet.com:8888. The firewall settings control how the firewall filters and allows network traffic based on rules and policies. The firewall settings may be blocking or preventing the access to the internal site by mistake or by default, especially if the site uses a non-standard port number such as 8888. The technician should check and modify the firewall settings to allow the access to the internal site or its port number. Default gateway settings determine how a computer connects to other networks or the internet. Default gateway settings are not likely to cause the issue of not being able to access an internal site if the user can access the public internet. DHCP settings determine how a computer obtains its IP address and other network configuration parameters automatically from a DHCP server. DHCP settings are not likely to cause the issue of not being able to access an internal site if the user can access other network resources. IP address settings determine how a computer identifies itself and communicates with other devices on a network. IP address settings are not likely to cause the issue of not being able to access an internal site if the user can access other network resources. Antivirus settings control how the antivirus software scans and protects the computer from malware and threats. Antivirus settings are less likely to cause the issue of not being able to access an internal site than firewall settings, unless the antivirus software has its own firewall feature that may interfere with the network traffic. References: CompTIA A+ Core 2 (220-1002) Certification Exam Objectives Version 4.0, Domain 1.6
A technician needs to recommend the best backup method that will mitigate ransomware attacks. Only a few files are regularly modified, however, storage space is a concern.
Which of the following backup methods would BEST address these concerns?
- A . Full
- B . Differential
- C . Off-site
- D . Grandfather-father-son
B
Explanation:
The differential backup method would best address these concerns. Differential backups only back up files that have changed since the last full backup, which means that only a few files would be backed up each time. This would help to mitigate the risk of ransomware attacks, as only a few files would be affected if an attack occurred. Additionally, differential backups require less storage space than full backups.
A user is unable to access a website, which is widely used across the organization, and receives the following error message:
The security certificate presented by this website has expired or is not yet valid.
The technician confirms the website works when accessing it from another computer but not from the user’s computer.
Which of the following should the technician perform NEXT to troubleshoot the issue?
- A . Reboot the computer.
- B . Reinstall the OS.
- C . Configure a static 12
- D . Check the computer’s date and time.
D
Explanation:
The error message indicates that the security certificate presented by the website has either expired or is not yet valid. This can happen if the computer’s clock has the wrong date or time, as SSL/TLS certificates have a specific validity period. If the clock is off by too much, it may cause the certificate to fail to validate. Therefore, the technician should check the computer’s date and time and ensure that they are correct.
Once weekly a user needs Linux to run a specific open-source application that is not available for the currently installed Windows platform. The user has limited bandwidth throughout the day.
Which of the following solutions would be the MOST efficient, allowing for parallel execution of the Linux application and Windows applications?
- A . Install and run Linux and the required application in a PaaS cloud environment
- B . Install and run Linux and the required application as a virtual machine installed under the Windows OS
- C . Use a swappable drive bay for the boot drive and install each OS with applications on its own drive Swap the drives as needed
- D . Set up a dual boot system by selecting the option to install Linux alongside Windows
B
Explanation:
The user should install and run Linux and the required application as a virtual machine installed under the Windows OS. This solution would allow for parallel execution of the Linux application and Windows applications2.
The MOST efficient solution that allows for parallel execution of the Linux application and Windows applications is to install and run Linux and the required application as a virtual machine installed under the Windows OS. This is because it allows you to run both Linux and Windows together without the need to keep the Linux portion confined to a VM window 3.
The network was breached over the weekend System logs indicate that a single user’s account was successfully breached after 500 attempts with a dictionary attack.
Which of the following would BEST mitigate this threat?
- A . Encryption at rest
- B . Account lockout
- C . Automatic screen lock
- D . Antivirus
B
Explanation:
Account lockout would best mitigate the threat of a dictionary attack1
A technician is setting up a backup method on a workstation that only requires two sets of tapes to restore.
Which of the following would BEST accomplish this task?
- A . Differential backup
- B . Off-site backup
- C . Incremental backup
- D . Full backup
A
Explanation:
HOTSPOT
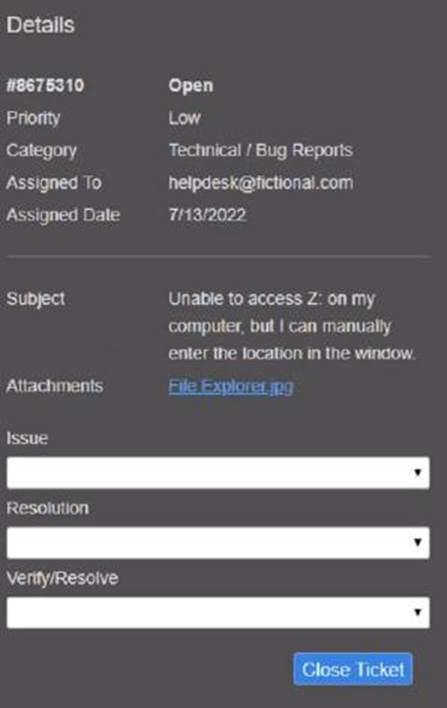
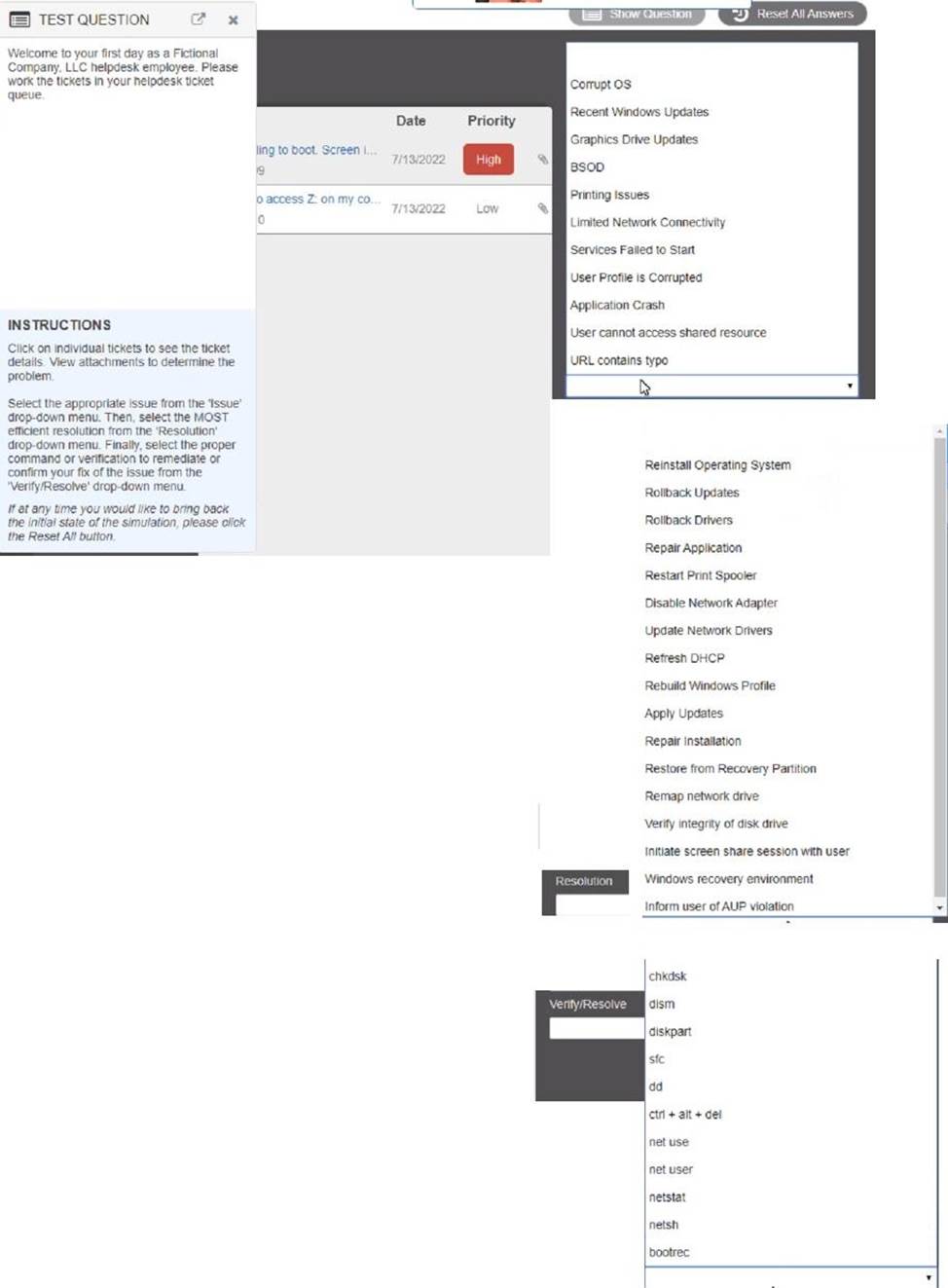
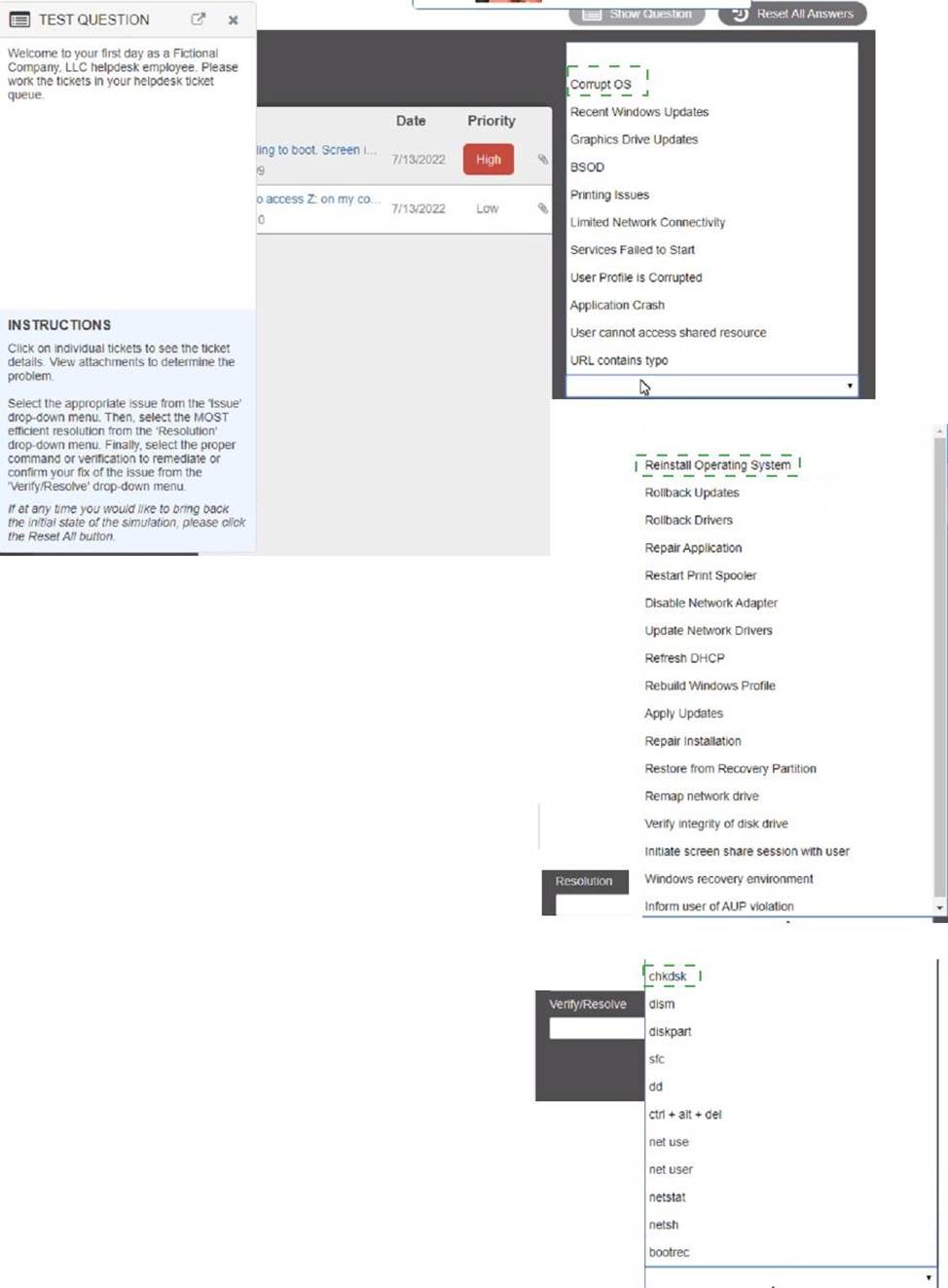
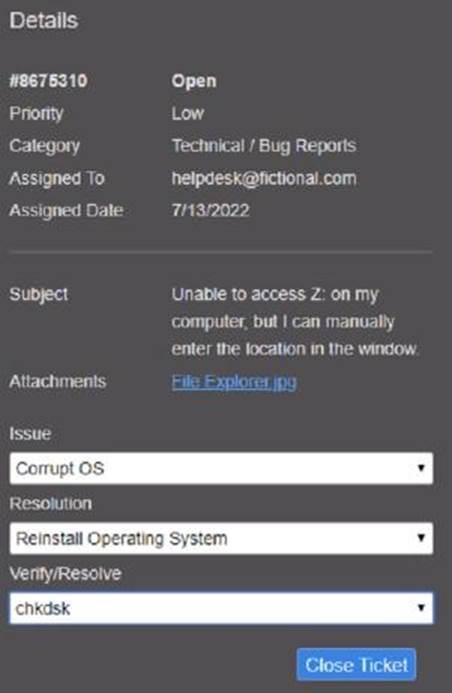
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the ‘issue’ drop-down menu. Then, select the MOST efficient resolution from the ‘Resolution’ drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
Explanation:
Graphical user interface, text, application
Description automatically generated
Latest 220-1102 Dumps Valid Version with 81 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

