Cisco 350-201 Performing CyberOps Using Core Security Technologies (CBRCOR) Online Training
Cisco 350-201 Online Training
The questions for 350-201 were last updated at Apr 16,2026.
- Exam Code: 350-201
- Exam Name: Performing CyberOps Using Core Security Technologies (CBRCOR)
- Certification Provider: Cisco
- Latest update: Apr 16,2026
Which bash command will print all lines from the “colors.txt” file containing the non case-sensitive pattern “Yellow”?
- A . grep -i “yellow” colors.txt
- B . locate “yellow” colors.txt
- C . locate -i “Yellow” colors.txt
- D . grep “Yellow” colors.txt
An engineer is moving data from NAS servers in different departments to a combined storage database so that the data can be accessed and analyzed by the organization on-demand .
Which data management process is being used?
- A . data clustering
- B . data regression
- C . data ingestion
- D . data obfuscation
A security manager received an email from an anomaly detection service, that one of their contractors has downloaded 50 documents from the company’s confidential document management folder using a company- owned asset al039-ice-4ce687TL0500. A security manager reviewed the content of downloaded documents and noticed that the data affected is from different departments .
What are the actions a security manager should take?
- A . Measure confidentiality level of downloaded documents.
- B . Report to the incident response team.
- C . Escalate to contractor’s manager.
- D . Communicate with the contractor to identify the motives.
A security analyst receives an escalation regarding an unidentified connection on the Accounting A1 server within a monitored zone. The analyst pulls the logs and discovers that a Powershell process and a WMI tool process were started on the server after the connection was established and that a PE format file was created in the system directory .
What is the next step the analyst should take?
- A . Isolate the server and perform forensic analysis of the file to determine the type and vector of a possible attack
- B . Identify the server owner through the CMDB and contact the owner to determine if these were planned and identifiable activities
- C . Review the server backup and identify server content and data criticality to assess the intrusion risk
- D . Perform behavioral analysis of the processes on an isolated workstation and perform cleaning procedures if the file is malicious
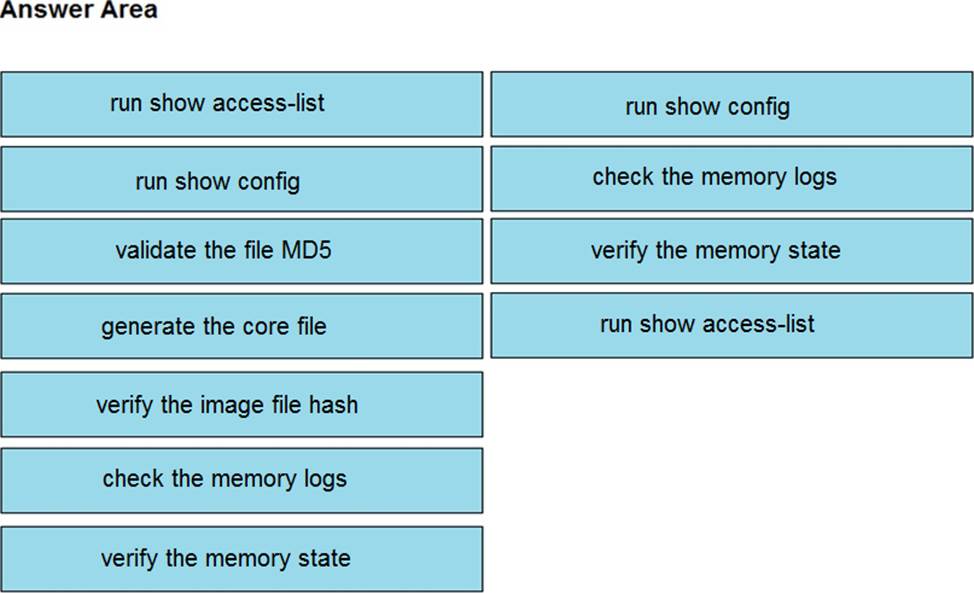
DRAG DROP
An organization lost connectivity to critical servers, and users cannot access business applications and internal websites. An engineer checks the network devices to investigate the outage and determines that all devices are functioning.
Drag and drop the steps from the left into the sequence on the right to continue investigating this issue. Not all options are used.
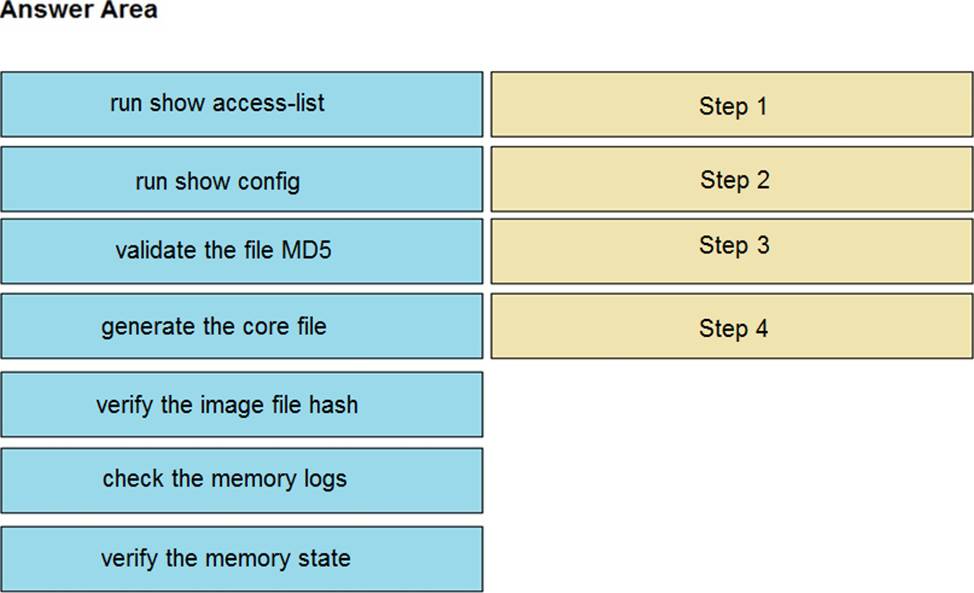
Refer to the exhibit.
Two types of clients are accessing the front ends and the core database that manages transactions, access control, and atomicity .
What is the threat model for the SQL database?
- A . An attacker can initiate a DoS attack.
- B . An attacker can read or change data.
- C . An attacker can transfer data to an external server.
- D . An attacker can modify the access logs.
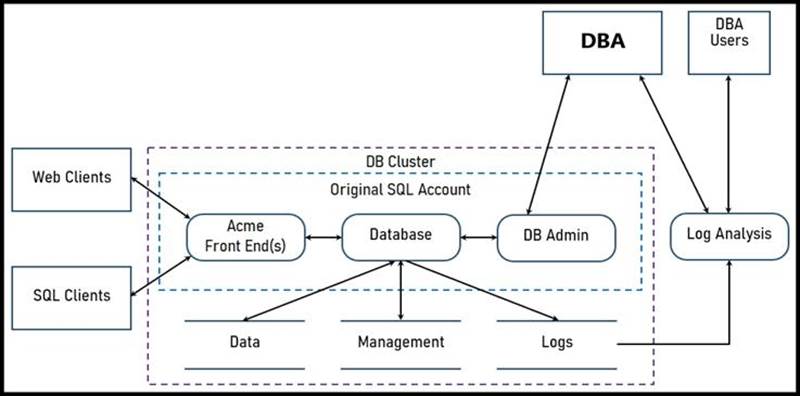
Refer to the exhibit.
An engineer must tune the Cisco IOS device to mitigate an attack that is broadcasting a large number of ICMP packets. The attack is sending the victim’s spoofed source IP to a network using an IP broadcast address that causes devices in the network to respond back to the source IP address .
Which action does the engineer recommend?
- A . Use command ip verify reverse-path interface
- B . Use global configuration command service tcp-keepalives-out
- C . Use subinterface command no ip directed-broadcast
- D . Use logging trap 6
Refer to the exhibit.
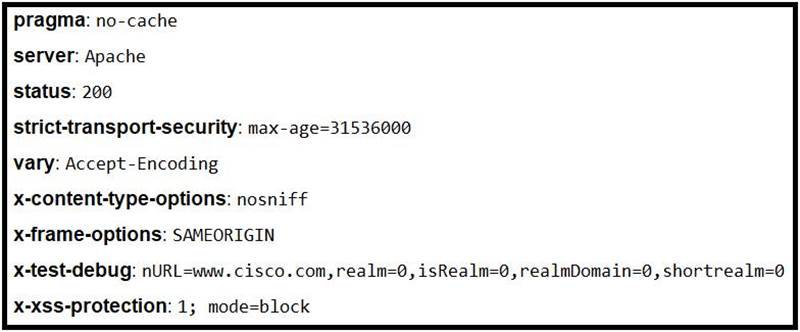
Where is the MIME type that should be followed indicated?
- A . x-test-debug
- B . strict-transport-security
- C . x-xss-protection
- D . x-content-type-options
Refer to the exhibit.
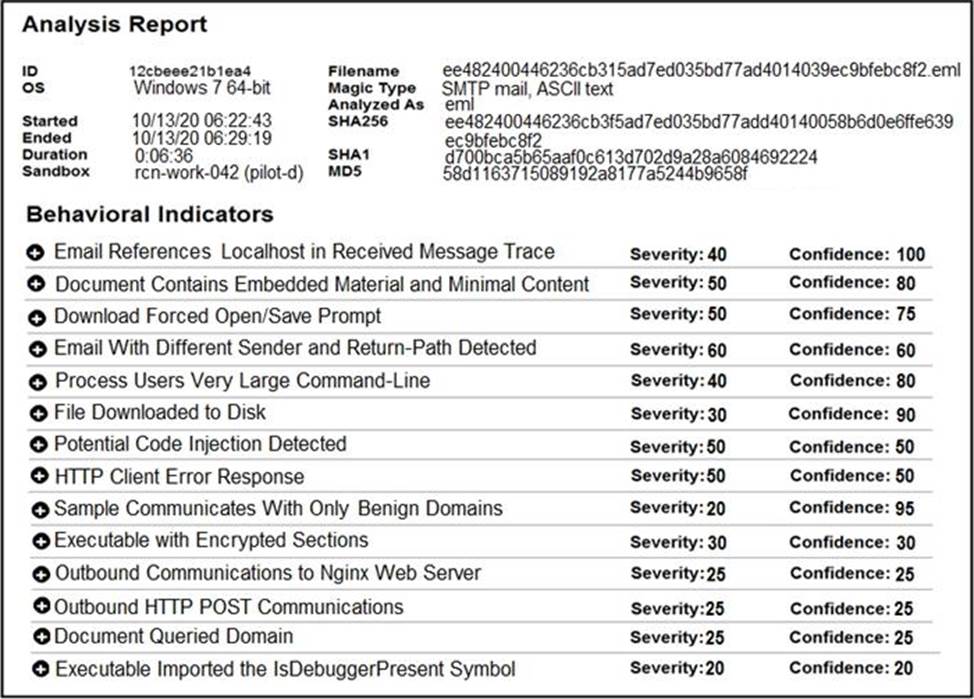
Cisco Advanced Malware Protection installed on an end-user desktop automatically submitted a low prevalence file to the Threat Grid analysis engine .
What should be concluded from this report?
- A . Threat scores are high, malicious ransomware has been detected, and files have been modified
- B . Threat scores are low, malicious ransomware has been detected, and files have been modified
- C . Threat scores are high, malicious activity is detected, but files have not been modified
- D . Threat scores are low and no malicious file activity is detected
An engineer implemented a SOAR workflow to detect and respond to incorrect login attempts and anomalous user behavior. Since the implementation, the security team has received dozens of false positive alerts and negative feedback from system administrators and privileged users. Several legitimate users were tagged as a threat and their accounts blocked, or credentials reset because of unexpected login times and incorrectly typed credentials .
How should the workflow be improved to resolve these issues?
- A . Meet with privileged users to increase awareness and modify the rules for threat tags
and anomalous behavior alerts - B . Change the SOAR configuration flow to remove the automatic remediation that is increasing the false positives and triggering threats
- C . Add a confirmation step through which SOAR informs the affected user and asks them to confirm whether they made the attempts
- D . Increase incorrect login tries and tune anomalous user behavior not to affect privileged accounts
Latest 350-201 Dumps Valid Version with 139 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund