Check Point 156-215.80 Check Point Certified Security Administrator R80 Online Training
Check Point 156-215.80 Online Training
The questions for 156-215.80 were last updated at Aug 13,2025.
- Exam Code: 156-215.80
- Exam Name: Check Point Certified Security Administrator R80
- Certification Provider: Check Point
- Latest update: Aug 13,2025
Packages and licenses are loaded from all of these sources EXCEPT
- A . Download Center Web site
- B . UserUpdate
- C . User Center
- D . Check Point DVD
Which of the following technologies extracts detailed information from packets and stores that information in state tables?
- A . INSPECT Engine
- B . Stateful Inspection
- C . Packet Filtering
- D . Application Layer Firewall
On the following graphic, you will find layers of policies.
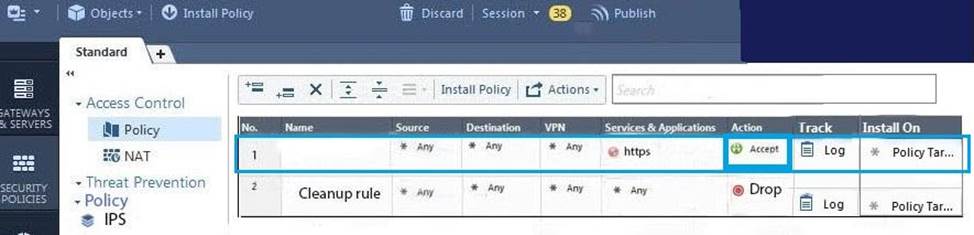
What is a precedence of traffic inspection for the defined polices?
- A . A packet arrives at the gateway, it is checked against the rules in the networks policy layer and then if Implicit Drop Rule drops the packet, it comes next to IPS layer and then after accepting the packet it passes to Threat Prevention layer.
- B . A packet arrives at the gateway, it is checked against the rules in the networks policy layer and then if there is any rule which accepts the packet, it comes next to IPS layer and then after accepting the packet it passes to Threat Prevention layer
- C . A packet arrives at the gateway, it is checked against the rules in the networks policy layer and then if there is any rule which accepts the packet, it comes next to Threat Prevention layer and then after accepting the packet it passes to IPS layer.
- D . A packet arrives at the gateway, it is checked against the rules in IPS policy layer and then if it is accepted then it comes next to the Network policy layer and then after accepting the packet it passes to Threat Prevention layer.
Tina is a new administrator who is currently reviewing the new Check Point R80 Management console interface.
In the Gateways view, she is reviewing the Summary screen as in the screenshot below.
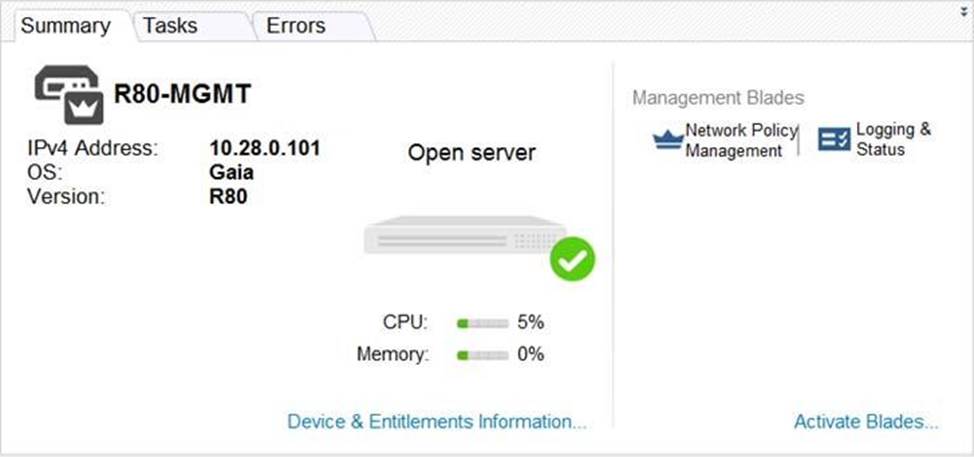
What as an ‘Open Server’?
- A . Check Point software deployed on a non-Check Point appliance.
- B . The Open Server Consortium approved Server Hardware used for the purpose of Security and Availability.
- C . A Check Point Management Server deployed using the Open Systems Interconnection (OSI) Server and Security deployment model.
- D . A Check Point Management Server software using the Open SSL.
Choose what BEST describes the Policy Layer Traffic Inspection.
- A . If a packet does not match any of the inline layers, the matching continues to the next Layer.
- B . If a packet matches an inline layer, it will continue matching the next layer.
- C . If a packet does not match any of the inline layers, the packet will be matched against the Implicit Clean-up Rule.
- D . If a packet does not match a Network Policy Layer, the matching continues to its inline layer.
What are the three conflict resolution rules in the Threat Prevention Policy Layers?
- A . Conflict on action, conflict on exception, and conflict on settings
- B . Conflict on scope, conflict on settings, and conflict on exception
- C . Conflict on settings, conflict on address, and conflict on exception
- D . Conflict on action, conflict on destination, and conflict on settings
What does the “unknown” SIC status shown on SmartConsole mean?
- A . The SMS can contact the Security Gateway but cannot establish Secure Internal Communication.
- B . SIC activation key requires a reset.
- C . The SIC activation key is not known by any administrator.
- D . There is no connection between the Security Gateway and SMS.
Kofi, the administrator of the ALPHA Corp network wishes to change the default Gaia WebUI Portal port number currently set on the default HTTPS port.
Which CLISH commands are required to be able to change this TCP port?
- A . set web ssl-port <new port number>
- B . set Gaia-portal port <new port number>
- C . set Gaia-portal https-port <new port number>
- D . set web https-port <new port number>
Browser-based Authentication sends users to a web page to acquire identities using ________ .
- A . User Directory
- B . Captive Portal and Transparent Kerberos Authentication
- C . Captive Portal
- D . UserCheck
Browser-based Authentication sends users to a web page to acquire identities using ________ .
- A . User Directory
- B . Captive Portal and Transparent Kerberos Authentication
- C . Captive Portal
- D . UserCheck
Latest 156-215.80 Dumps Valid Version with 528 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund