Amazon SCS-C01 AWS Certified Security Specialty Online Training
Amazon SCS-C01 Online Training
The questions for SCS-C01 were last updated at May 15,2024.
- Exam Code: SCS-C01
- Exam Name: AWS Certified Security Specialty
- Certification Provider: Amazon
- Latest update: May 15,2024
A company’s Security Engineer has been asked to monitor and report all AWS account root user activities.
Which of the following would enable the Security Engineer to monitor and report all root user activities? (Select TWO)
- A . Configuring AWS Organizations to monitor root user API calls on the paying account
- B . Creating an Amazon CloudWatch Events rule that will trigger when any API call from the root user is reported
- C . Configuring Amazon Inspector to scan the AWS account for any root user activity
- D . Configuring AWS Trusted Advisor to send an email to the Security team when the root user logs in to the console
- E . Using Amazon SNS to notify the target group
A company Is building a data lake on Amazon S3. The data consists of millions of small files containing sensitive information.
The security team has the following requirements for the architecture:
• Data must be encrypted in transit.
• Data must be encrypted at rest.
• The bucket must be private, but if the bucket is accidentally made public, the data must remain confidential.
Which combination of steps would meet the requirements? (Select THREE.)
- A . Enable AES-256 encryption using server-side encryption with Amazon S3-managed encryption keys (SSE-S3) on the S3 bucket
- B . Enable default encryption with server-side encryption with AWS KMS-managed keys (SSE-KMS) on the S3 bucket.
- C . Add a bucket policy that includes a deny if a PutObject request does not include awsiSecureTcanspoct.
- D . Add a bucket policy with ws: Sourcelpto Allow uploads and downloads from the corporate intranet only.
- E . Add a bucket policy that includes a deny if a PutObject request does not include s3:x-amz-sairv9r-side-enctyption: "aws: kms".
- F . Enable Amazon Macie to monitor and act on changes to the data lake’s S3 bucket.
A recent security audit identified that a company’s application team injects database credentials into the environment variables of an AWS Fargate task. The company’s security policy mandates that all sensitive data be encrypted at rest and in transit.
When combination of actions should the security team take to make the application compliant within the security policy? (Select THREE)
- A . Store the credentials securely in a file in an Amazon S3 bucket with restricted access to the application team IAM role Ask the application team to read the credentials from the S3 object instead
- B . Create an AWS Secrets Manager secret and specify the key/value pairs to be stored in this secret
- C . Modify the application to pull credentials from the AWS Secrets Manager secret instead of the environment variables.
- D . Add the following statement to the container instance IAM role policy
- E . Add the following statement to the execution role policy.
- F . Log in to the AWS Fargate instance, create a script to read the secret value from AWS Secret Manager, and inject the environment variables. Ask the application team to redeploy the application.
A company is designing the securely architecture (or a global latency-sensitive web application it plans to deploy to AWS. A Security Engineer needs to configure a highly available and secure two-tier architecture. The security design must include controls to prevent common attacks such as DDoS, cross-site scripting, and SQL injection.
Which solution meets these requirements?
- A . Create an Application Load Balancer (ALB) that uses public subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create an Amazon
CloudFront distribution that uses the ALB as its origin. Create appropriate AWS WAF ACLs and enable them on the CloudFront distribution. - B . Create an Application Load Balancer (ALB) that uses private subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create an Amazon CloudFront distribution that uses the ALB as its origin. Create appropriate AWS WAF ACLs and enable them on the CloudFront distribution.
- C . Create an Application Load Balancer (ALB) that uses public subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create appropriate AWS WAF ACLs and enable them on the ALB.
- D . Create an Application Load Balancer (ALB) that uses private subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create appropriate AWS WAF ACLs and enable them on the ALB.
A company is running an application on Amazon EC2 instances in an Auto Scaling group. The application stores logs locally A security engineer noticed that logs were lost after a scale-in event. The security engineer needs to recommend a solution to ensure the durability and availability of log data All logs must be kept for a minimum of 1 year for auditing purposes.
What should the security engineer recommend?
- A . Within the Auto Scaling lifecycle, add a hook to create and attach an Amazon Elastic Block Store (Amazon EBS) log volume each time an EC2 instance is created. When the instance is terminated, the EBS volume can be reattached to another instance for log review.
- B . Create an Amazon Elastic File System (Amazon EFS) file system and add a command in the user data section of the Auto Scaling launch template to mount the EFS file system during EC2 instance creation Configure a process on the instance to copy the logs once a day from an instance Amazon Elastic Block Store (Amazon EBS) volume to a directory in the EFS file system.
- C . Build the Amazon CloudWatch agent into the AMI used in the Auto Scaling group. Configure the CloudWatch agent to send the logs to Amazon CloudWatch Logs for review.
- D . Within the Auto Scaling lifecycle, add a lifecycle hook at the terminating state transition and alert the engineering team by using a lifecycle notification to Amazon Simple Notification Service (Amazon SNS). Configure the hook to remain in the Terminating: Wait state for 1 hour to allow manual review of the security logs prior to instance termination.
A company has multiple production AWS accounts. Each account has AWS CloudTrail configured to log to a single Amazon S3 bucket in a central account. Two of the production accounts have trails that are not logging anything to the S3 bucket.
Which steps should be taken to troubleshoot the issue? (Choose three.)
- A . Verify that the log file prefix is set to the name of the S3 bucket where the logs should go.
- B . Verify that the S3 bucket policy allows access for CloudTrail from the production AWS account IDs.
- C . Create a new CloudTrail configuration in the account, and configure it to log to the account’s S3 bucket.
- D . Confirm in the CloudTrail Console that each trail is active and healthy.
- E . Open the global CloudTrail configuration in the master account, and verify that the storage location is set to the correct S3 bucket.
- F . Confirm in the CloudTrail Console that the S3 bucket name is set correctly.
A company has several workloads running on AWS Employees are required to authenticate using on-premises ADFS and SSO to access the AWS Management Console Developers migrated an existing legacy web application to an Amazon EC2 instance Employees need to access this application from anywhere on the internet but currently, mere is no authentication system but into the application.
How should the Security Engineer implement employee-only access to this system without changing the application?
- A . Place the application behind an Application Load Balancer (ALB) Use Amazon Cognito as authentication (or the ALB Define a SAML-based Amazon Cognito user pool and connect it to ADFS
implement AWS SSO in the master account and link it to ADFS as an identity provide’ Define the EC2 instance as a managed resource, then apply an IAM policy on the resource - B . Define an Amazon Cognito identity pool then install the connector on the Active Directory server Use the Amazon Cognito SDK on the application instance to authenticate the employees using their
- C . Active Directory user names and passwords
- D . Create an AWS Lambda custom authorizer as the authenticator for a reverse proxy on Amazon EC2 Ensure the security group on Amazon EC2 only allows access from the Lambda function.
A company has a website with an Amazon CloudFront HTTPS distribution, an Application Load Balancer (ALB) with multiple web instances for dynamic website content, and an Amazon S3 bucket for static website content.
The company’s security engineer recently updated the website security requirements:
• HTTPS needs to be enforced for all data in transit with specific ciphers.
• The CloudFront distribution needs to be accessible from the internet only.
Which solution will meet these requirements?
Set up an S3 bucket policy with the awssecuretransport key Configure the CloudFront origin access identity (OAI) with the S3 bucket Configure CloudFront to use specific ciphers. Enforce the ALB with an HTTPS listener only and select the appropriate security policy for the ciphers Link the ALB with AWS WAF to allow access from the CloudFront IP ranges.
Set up an S3 bucket policy with the aws:securetransport key. Configure the CloudFront origin access identity (OAI) with the S3 bucket. Enforce the ALB with an HTTPS listener only and select the appropriate security policy for the ciphers.
Modify the CloudFront distribution to use AWS WAF. Force HTTPS on the S3 bucket with specific ciphers in the bucket policy. Configure an HTTPS listener only for the ALB. Set up a security group to limit access to the ALB from the CloudFront IP ranges
Modify the CloudFront distribution to use the ALB as the origin. Enforce an HTTPS listener on the ALB. Create a path-based routing rule on the ALB with proxies that connect lo Amazon S3. Create a bucket policy to allow access from these proxies only.
A company Is trying to replace its on-premises bastion hosts used to access on-premises Linux servers with AWS Systems Manager Session Manager. A security engineer has installed the Systems Manager Agent on all servers. The security engineer verifies that the agent is running on all the servers, but Session Manager cannot connect to them. The security engineer needs to perform verification steps before Session Manager will work on the servers.
Which combination of steps should the security engineer perform? (Select THREE.)
- A . Open inbound port 22 to 0 0.0.0/0 on all Linux servers.
- B . Enable the advanced-instances tier in Systems Manager.
- C . Create a managed-instance activation for the on-premises servers.
- D . Reconfigure the Systems Manager Agent with the activation code and ID.
- E . Assign an IAM role to all of the on-premises servers.
- F . Initiate an inventory collection with Systems Manager on the on-premises servers
A company has recently recovered from a security incident that required the restoration of Amazon EC2 instances from snapshots.
After performing a gap analysis of its disaster recovery procedures and backup strategies, the company is concerned that, next time, it will not be able to recover the EC2 instances if the AWS account was compromised and Amazon EBS snapshots were deleted.
All EBS snapshots are encrypted using an AWS KMS CMK.
Which solution would solve this problem?
- A . Create a new Amazon S3 bucket Use EBS lifecycle policies to move EBS snapshots to
the new S3 bucket. Move snapshots to Amazon S3 Glacier using lifecycle policies, and apply Glacier Vault Lock policies to prevent deletion - B . Use AWS Systems Manager to distribute a configuration that performs local backups of all attached disks to Amazon S3.
- C . Create a new AWS account with limited privileges. Allow the new account to access the AWS KMS key used to encrypt the EBS snapshots, and copy the encrypted snapshots to the new account on a recuning basis
- D . Use AWS Backup to copy EBS snapshots to Amazon S3.
A Security Engineer manages AWS Organizations for a company. The Engineer would like to restrict AWS usage to allow Amazon S3 only in one of the organizational units (OUs).
The Engineer adds the following SCP to the OU:
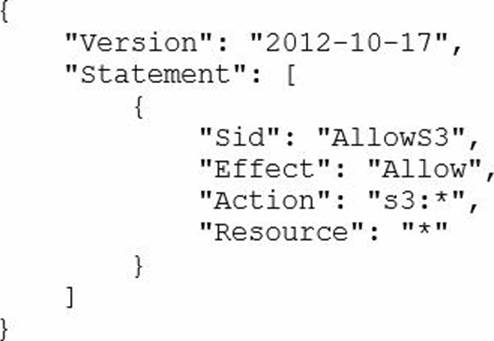
The next day. API calls to AWS IAM appear in AWS CloudTrail logs In an account under that OU.
How should the Security Engineer resolve this issue?
- A . Move the account to a new OU and deny IAM:* permissions.
- B . Add a Deny policy for all non-S3 services at the account level.
- C . Change the policy to:

- D . Detach the default FullAWSAccess SCP
Latest SCS-C01 Dumps Valid Version with 470 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

