Topic 1, Exam Pool OCT
A company’s security team has defined a set of AWS Config rules that must be enforced globally in all AWS accounts the company owns.
What should be done to provide a consolidated compliance overview for the security team?
- A . Use AWS Organizations to limit AWS Config rules to the appropriate Regions, and then consolidate the Amazon CloudWatch dashboard into one AWS account.
- B . Use AWS Config aggregation to consolidate the views into one AWS account, and provide role access to the security team.
- C . Consolidate AWS Config rule results with an AWS Lambda function and push data to Amazon SQS. Use Amazon SNS to consolidate and alert when some metrics are triggered.
- D . Use Amazon GuardDuty to load data results from the AWS Config rules compliance status, aggregate GuardDuty findings of all AWS accounts into one AWS account, and provide role access to the security team.
A security engineer is designing an incident response plan to address the risk of a compromised Amazon EC2 instance.
The plan must recommend a solution to meet the following requirements:
• A trusted forensic environment must be provisioned
• Automated response processes must be orchestrated
Which AWS services should be included in the plan? {Select TWO)
- A . AWS CloudFormation
- B . Amazon GuardDuty
- C . Amazon Inspector
- D . Amazon Macie
- E . AWS Step Functions
A security engineer has been tasked with implementing a solution that allows the company’s development team to have interactive command line access to Amazon EC2 Linux instances using the AWS Management Console.
Which steps should the security engineer take to satisfy this requirement while maintaining least privilege?
- A . Enable AWS Systems Manager in the AWS Management Console and configure for access to EC2 instances using the default AmazonEC2RoleforSSM role. Install the Systems Manager Agent on all EC2 Linux instances that need interactive access. Configure IAM user policies to allow development team access to the Systems Manager Session Manager and attach to the team’s IAM users.
- B . Enable console SSH access in the EC2 console. Configure IAM user policies to allow development team access to the AWS Systems Manager Session Manager and attach to the development team’s IAM users.
- C . Enable AWS Systems Manager in the AWS Management Console and configure to access EC2 instances using the default AmazonEC2RoleforSSM role. Install the Systems Manager Agent on all EC2 Linux instances that need interactive access. Configure a security group that allows SSH port 22 from all published IP addresses. Configure IAM user policies to allow development team access to the AWS Systems Manager Session Manager and attach to the team’s IAM users.
- D . Enable AWS Systems Manager in the AWS Management Console and configure to access EC2 instances using the default AmazonEC2RoleforSSM role Install the Systems Manager Agent on all EC2 Linux instances that need interactive access. Configure IAM policies to allow development team access to the EC2 console and attach to the teams IAM users.
A large government organization is moving to the cloud and has specific encryption requirements. The first workload to move requires that a customer’s data be immediately destroyed when the customer makes that request.
Management has asked the security team to provide a solution that will securely store the data, allow only authorized applications to perform encryption and decryption and allow for immediate destruction of the data
Which solution will meet these requirements?
- A . Use AWS Secrets Manager and an AWS SDK to create a unique secret for the customer-specific data
- B . Use AWS Key Management Service (AWS KMS) and the AWS Encryption SDK to
generate and store a data encryption key for each customer. - C . Use AWS Key Management Service (AWS KMS) with service-managed keys to generate and store customer-specific data encryption keys
- D . Use AWS Key Management Service (AWS KMS) and create an AWS CloudHSM custom key store Use CloudHSM to generate and store a new CMK for each customer.
Unapproved changes were previously made to a company’s Amazon S3 bucket. A security engineer configured AWS Config to record configuration changes made to the company’s S3 buckets. The engineer discovers there are S3 configuration changes being made, but no Amazon SNS notifications are being sent. The engineer has already checked the configuration of the SNS topic and has confirmed the configuration is valid.
Which combination of steps should the security engineer take to resolve the issue? (Select TWO.)
- A . Configure the S3 bucket ACLs to allow AWS Config to record changes to the buckets.
- B . Configure policies attached to S3 buckets to allow AWS Config to record changes to the buckets.
- C . Attach the AmazonS3ReadOnryAccess managed policy to the IAM user.
- D . Verify the security engineer’s IAM user has an attached policy that allows all AWS Config actions.
- E . Assign the AWSConfigRole managed policy to the AWS Config role
A company is operating an open-source software platform that is internet facing. The legacy software platform no longer receives security updates. The software platform operates using Amazon route 53 weighted load balancing to send traffic to two Amazon EC2 instances that connect to an Amazon POS cluster a recent report suggests this software platform is vulnerable to SQL injection attacks. with samples of attacks provided. The company’s security engineer must secure this system against SQL injection attacks within 24 hours. The secure, engineer’s solution involve the least amount of effort and maintain normal operations during implementation.
What should the security engineer do to meet these requirements?
- A . Create an Application Load Balancer with the existing EC2 instances as a target group Create an AWS WAF web ACL containing rules mat protect the application from this attach. then apply it to the ALB Test to ensure me vulnerability has been mitigated, then redirect thee Route 53 records to point to the ALB Update security groups on the EC 2 instances to prevent direct access from the internet
- B . Create an Amazon CloudFront distribution specifying one EC2 instance as an origin Create an AWS WAF web ACL containing rules that protect the application from this attack, then apply it to me distribution Test to ensure the vulnerability has mitigated, then redirect the Route 53 records to point to CloudFront
- C . Obtain me latest source code for the platform and make ire necessary updates Test me updated code to ensure that the vulnerability has been irrigated, then deploy me patched version of the platform to the EC2 instances
- D . Update the security group mat is attached to the EC2 instances, removing access from the internet to the TCP port used by the SQL database Create an AWS WAF web ACL containing rules mat protect me application from this attack, men apply it to the EC2 instances Test to ensure me vulnerability has been mitigated. then restore the security group to me onginal setting
A company is using AWS Organizations to manage multiple AWS accounts. The company has an application that allows users to assume the AppUser IAM role to download files from an Amazon S3 bucket that is encrypted with an AWS KMS CMK However when users try to access the files in the S3 bucket they get an access denied error.
What should a Security Engineer do to troubleshoot this error? (Select THREE)
- A . Ensure the KMS policy allows the AppUser role to have permission to decrypt for the CMK
- B . Ensure the S3 bucket policy allows the AppUser role to have permission to get objects for the S3 bucket
- C . Ensure the CMK was created before the S3 bucket.
- D . Ensure the S3 block public access feature is enabled for the S3 bucket.
- E . Ensure that automatic key rotation is disabled for the CMK
- F . Ensure the SCPs within Organizations allow access to the S3 bucket.
A security engineer has noticed that VPC Flow Logs are getting a lot REJECT traffic originating from a single Amazon EC2 instance in an Auto Scaling group. The security engineer is concerned that this EC2 instance may be compromised.
What immediate action should the security engineer take?
- A . Remove me instance from the Auto Seating group Close me security group mm ingress only from a single forensic P address to perform an analysis.
- B . Remove me instance from the Auto Seating group Change me network ACL rules to allow traffic only from a single forensic IP address to perform en analysis Add a rule to deny all other traffic.
- C . Remove the instance from the Auto Scaling group Enable Amazon GuardDuty in that AWS account Install the Amazon Inspector agent cm the suspicious EC 2 instance to perform a scan.
- D . Take a snapshot of the suspicious EC2 instance. Create a new EC2 instance from me snapshot in a closed security group with ingress only from a single forensic IP address to perform an analysis
A company is collecting AWS CloudTrail log data from multiple AWS accounts by managing individual trails in each account and forwarding log data to a centralized Amazon S3 bucket residing in a log archive account. After CloudTrail introduced support for AWS Organizations trails, the company decided to further centralize management and automate deployment of the CloudTrail logging capability across all of its AWS accounts.
The company’s security engineer created an AWS Organizations trail in the master account, enabled server-side encryption with AWS KMS managed keys (SSE-KMS) for the log files, and specified the same bucket as the storage location. However, the engineer noticed that logs recorded by the new trail were not delivered to the bucket.
Which factors could cause this issue? (Select TWO.)
- A . The CMK key policy does not allow CloudTrail to make encrypt and decrypt API calls against the key.
- B . The CMK key policy does not allow CloudTrail to make GenerateDataKey API calls against the key.
- C . The IAM role used by the CloudTrail trail does not have permissions to make PutObject API calls against a folder created for the Organizations trail.
- D . The S3 bucket policy does not allow CloudTrail to make PutObject API calls against a folder created for the Organizations trail.
- E . The CMK key policy does not allow the IAM role used by the CloudTrail trail to use the key for crypto graphicaI operations.
Which of the following are valid configurations for using SSL certificates with Amazon CloudFront? (Select THREE)
- A . Default AWS Certificate Manager certificate
- B . Custom SSL certificate stored in AWS KMS
- C . Default CloudFront certificate
- D . Custom SSL certificate stored in AWS Certificate Manager
- E . Default SSL certificate stored in AWS Secrets Manager
- F . Custom SSL certificate stored in AWS IAM
A company has implemented centralized logging and monitoring of AWS CloudTrail logs from all Regions in an Amazon S3 bucket. The log Hies are encrypted using AWS KMS. A Security Engineer is attempting to review the log files using a third-party tool hosted on an Amazon EC2 instance. The Security Engineer is unable to access the logs in the S3 bucket and receives an access denied error message.
What should the Security Engineer do to fix this issue?
- A . Check that the role the Security Engineer uses grants permission to decrypt objects using the KMS CMK.
- B . Check that the role the Security Engineer uses grants permission to decrypt objects using the KMS CMK and gives access to the S3 bucket and objects
- C . Check that the role the EC2 instance profile uses grants permission lo decrypt objects using the KMS CMK and gives access to the S3 bucket and objects
- D . Check that the role the EC2 instance profile uses grants permission to decrypt objects using the KMS CMK
A company has a VPC with several Amazon EC2 instances behind a NAT gateway. The company’s security policy states that all network traffic must be logged and must include the original source and destination IP addresses. The existing VPC Flow Logs do not include this information. A security engineer needs to recommend a solution.
Which combination of steps should the security engineer recommend? (Select TWO)
- A . Edit the existing VPC Flow Logs. Change the log format of the VPC Flow Logs from the Amazon default format to a custom format.
- B . Delete and recreate the existing VPC Flow Logs. Change the log format of the VPC Flow Logs from the Amazon default format to a custom format.
- C . Change the destination to Amazon CloudWatch Logs.
- D . Include the pkt-srcaddr and pkt-dstaddr fields in the log format.
- E . Include the subnet-id and instance-id fields in the log format.
A company recently performed an annual security assessment of its AWS environment. The assessment showed that audit logs are not available beyond 90 days and that unauthorized changes to IAM policies are made without detection.
How should a security engineer resolve these issues?
- A . Create an Amazon S3 lifecycle policy that archives AWS CloudTrail trail logs to Amazon S3 Glacier after 90 days. Configure Amazon Inspector to provide a notification when a policy change is made to resources.
- B . Configure AWS Artifact to archive AWS CloudTrail logs Configure AWS Trusted Advisor to provide a notification when a policy change is made to resources.
- C . Configure Amazon CloudWatch to export log groups to Amazon S3. Configure AWS CloudTrail to provide a notification when a policy change is made to resources.
- D . Create an AWS CloudTrail trail that stores audit logs in Amazon S3. Configure an AWS Config rule to provide a notif cation when a policy change is made to resources.
A company has several critical applications running on a large fleet of Amazon EC2 instances. As part of a security operations review, the company needs to apply a critical operating system patch to EC2 instances within 24 hours of the patch becoming available from the operating system vendor. The company does not have a patching solution deployed on AWS, but does have AWS Systems Manager configured. The solution must also minimize administrative overhead.
What should a security engineer recommend to meet these requirements?
- A . Create an AWS Config rule defining the patch as a required configuration for EC2 instances.
- B . Use the AWS Systems Manager Run Command to patch affected instances.
- C . Use an AWS Systems Manager Patch Manager predefined baseline to patch affected instances.
- D . Use AWS Systems Manager Session Manager to log in to each affected instance and apply the patch.
A security engineer is asked to update an AW3 CoudTrail log file prefix for an existing trail. When attempting to save the change in the CloudTrail console, the security engineer receives the following error message. "There is a problem with the bucket policy”
What will enable the security engineer to saw the change?
- A . Create a new trail with the updated log file prefix, and then delete the original nail Update the existing bucket policy in the Amazon S3 console with the new log the prefix, and then update the log file prefix in the CloudTrail console
- B . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform PutBucketPolicy. and then update the log file prefix in the CloudTrail console
- C . Update the existing bucket policy in the Amazon S3 console with the new log file prefix, and then update the log file prefix in the CloudTrail console.
- D . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform GetBucketPolicy, and then update the log file prefix in the CloudTrail console
A security engineer is asked to update an AW3 CoudTrail log file prefix for an existing trail. When attempting to save the change in the CloudTrail console, the security engineer receives the following error message. "There is a problem with the bucket policy”
What will enable the security engineer to saw the change?
- A . Create a new trail with the updated log file prefix, and then delete the original nail Update the existing bucket policy in the Amazon S3 console with the new log the prefix, and then update the log file prefix in the CloudTrail console
- B . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform PutBucketPolicy. and then update the log file prefix in the CloudTrail console
- C . Update the existing bucket policy in the Amazon S3 console with the new log file prefix, and then update the log file prefix in the CloudTrail console.
- D . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform GetBucketPolicy, and then update the log file prefix in the CloudTrail console
A security engineer is asked to update an AW3 CoudTrail log file prefix for an existing trail. When attempting to save the change in the CloudTrail console, the security engineer receives the following error message. "There is a problem with the bucket policy”
What will enable the security engineer to saw the change?
- A . Create a new trail with the updated log file prefix, and then delete the original nail Update the existing bucket policy in the Amazon S3 console with the new log the prefix, and then update the log file prefix in the CloudTrail console
- B . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform PutBucketPolicy. and then update the log file prefix in the CloudTrail console
- C . Update the existing bucket policy in the Amazon S3 console with the new log file prefix, and then update the log file prefix in the CloudTrail console.
- D . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform GetBucketPolicy, and then update the log file prefix in the CloudTrail console
A security engineer is asked to update an AW3 CoudTrail log file prefix for an existing trail. When attempting to save the change in the CloudTrail console, the security engineer receives the following error message. "There is a problem with the bucket policy”
What will enable the security engineer to saw the change?
- A . Create a new trail with the updated log file prefix, and then delete the original nail Update the existing bucket policy in the Amazon S3 console with the new log the prefix, and then update the log file prefix in the CloudTrail console
- B . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform PutBucketPolicy. and then update the log file prefix in the CloudTrail console
- C . Update the existing bucket policy in the Amazon S3 console with the new log file prefix, and then update the log file prefix in the CloudTrail console.
- D . Update the existing bucket policy in the Amazon S3 console to allow the security engineers principal to perform GetBucketPolicy, and then update the log file prefix in the CloudTrail console
The rule set in the virtual appliance is correct
Which of the following are other valid items to troubleshoot in this scenario? (Choose two.)
- A . Verify that the 0.0.0.0/0 route in the route table for the web server subnet points to a NAT gateway.
- B . Verify which Security Group is applied to the particular web server’s elastic network interface (ENI).
- C . Verify that the 0.0.0.0/0 route in the route table for the web server subnet points to the virtual security appliance.
- D . Verify the registered targets in the ALB.
- E . Verify that the 0.0.0.0/0 route in the public subnet points to a NAT gateway.
C,D
Explanation:
https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/using-eni.html
A Web Administrator for the website example.com has created an Amazon CloudFront distribution for dev.example.com, with a requirement to configure HTTPS using a custom TLS certificate imported to AWS Certificate Manager.
Which combination of steps is required to ensure availability of the certificate in the CloudFront console? (Choose two.)
- A . Call UploadServerCertificate with /cloudfront/dev/ in the path parameter.
- B . Import the certificate with a 4,096-bit RSA public key.
- C . Ensure that the certificate, private key, and certificate chain are PKCS #12-encoded.
- D . Import the certificate in the us-east-1 (N. Virginia) Region.
- E . Ensure that the certificate, private key, and certificate chain are PEM-encoded.
A company’s Security Engineer has been asked to monitor and report all AWS account root user activities.
Which of the following would enable the Security Engineer to monitor and report all root user activities? (Select TWO)
- A . Configuring AWS Organizations to monitor root user API calls on the paying account
- B . Creating an Amazon CloudWatch Events rule that will trigger when any API call from the root user is reported
- C . Configuring Amazon Inspector to scan the AWS account for any root user activity
- D . Configuring AWS Trusted Advisor to send an email to the Security team when the root user logs in to the console
- E . Using Amazon SNS to notify the target group
A company Is building a data lake on Amazon S3. The data consists of millions of small files containing sensitive information.
The security team has the following requirements for the architecture:
• Data must be encrypted in transit.
• Data must be encrypted at rest.
• The bucket must be private, but if the bucket is accidentally made public, the data must remain confidential.
Which combination of steps would meet the requirements? (Select THREE.)
- A . Enable AES-256 encryption using server-side encryption with Amazon S3-managed encryption keys (SSE-S3) on the S3 bucket
- B . Enable default encryption with server-side encryption with AWS KMS-managed keys (SSE-KMS) on the S3 bucket.
- C . Add a bucket policy that includes a deny if a PutObject request does not include awsiSecureTcanspoct.
- D . Add a bucket policy with ws: Sourcelpto Allow uploads and downloads from the corporate intranet only.
- E . Add a bucket policy that includes a deny if a PutObject request does not include s3:x-amz-sairv9r-side-enctyption: "aws: kms".
- F . Enable Amazon Macie to monitor and act on changes to the data lake’s S3 bucket.
A recent security audit identified that a company’s application team injects database credentials into the environment variables of an AWS Fargate task. The company’s security policy mandates that all sensitive data be encrypted at rest and in transit.
When combination of actions should the security team take to make the application compliant within the security policy? (Select THREE)
- A . Store the credentials securely in a file in an Amazon S3 bucket with restricted access to the application team IAM role Ask the application team to read the credentials from the S3 object instead
- B . Create an AWS Secrets Manager secret and specify the key/value pairs to be stored in this secret
- C . Modify the application to pull credentials from the AWS Secrets Manager secret instead of the environment variables.
- D . Add the following statement to the container instance IAM role policy
- E . Add the following statement to the execution role policy.
- F . Log in to the AWS Fargate instance, create a script to read the secret value from AWS Secret Manager, and inject the environment variables. Ask the application team to redeploy the application.
A company is designing the securely architecture (or a global latency-sensitive web application it plans to deploy to AWS. A Security Engineer needs to configure a highly available and secure two-tier architecture. The security design must include controls to prevent common attacks such as DDoS, cross-site scripting, and SQL injection.
Which solution meets these requirements?
- A . Create an Application Load Balancer (ALB) that uses public subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create an Amazon
CloudFront distribution that uses the ALB as its origin. Create appropriate AWS WAF ACLs and enable them on the CloudFront distribution. - B . Create an Application Load Balancer (ALB) that uses private subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create an Amazon CloudFront distribution that uses the ALB as its origin. Create appropriate AWS WAF ACLs and enable them on the CloudFront distribution.
- C . Create an Application Load Balancer (ALB) that uses public subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create appropriate AWS WAF ACLs and enable them on the ALB.
- D . Create an Application Load Balancer (ALB) that uses private subnets across multiple Availability Zones within a single Region. Point the ALB to an Auto Scaling group with Amazon EC2 instances in private subnets across multiple Availability Zones within the same Region. Create appropriate AWS WAF ACLs and enable them on the ALB.
A company is running an application on Amazon EC2 instances in an Auto Scaling group. The application stores logs locally A security engineer noticed that logs were lost after a scale-in event. The security engineer needs to recommend a solution to ensure the durability and availability of log data All logs must be kept for a minimum of 1 year for auditing purposes.
What should the security engineer recommend?
- A . Within the Auto Scaling lifecycle, add a hook to create and attach an Amazon Elastic Block Store (Amazon EBS) log volume each time an EC2 instance is created. When the instance is terminated, the EBS volume can be reattached to another instance for log review.
- B . Create an Amazon Elastic File System (Amazon EFS) file system and add a command in the user data section of the Auto Scaling launch template to mount the EFS file system during EC2 instance creation Configure a process on the instance to copy the logs once a day from an instance Amazon Elastic Block Store (Amazon EBS) volume to a directory in the EFS file system.
- C . Build the Amazon CloudWatch agent into the AMI used in the Auto Scaling group. Configure the CloudWatch agent to send the logs to Amazon CloudWatch Logs for review.
- D . Within the Auto Scaling lifecycle, add a lifecycle hook at the terminating state transition and alert the engineering team by using a lifecycle notification to Amazon Simple Notification Service (Amazon SNS). Configure the hook to remain in the Terminating: Wait state for 1 hour to allow manual review of the security logs prior to instance termination.
A company has multiple production AWS accounts. Each account has AWS CloudTrail configured to log to a single Amazon S3 bucket in a central account. Two of the production accounts have trails that are not logging anything to the S3 bucket.
Which steps should be taken to troubleshoot the issue? (Choose three.)
- A . Verify that the log file prefix is set to the name of the S3 bucket where the logs should go.
- B . Verify that the S3 bucket policy allows access for CloudTrail from the production AWS account IDs.
- C . Create a new CloudTrail configuration in the account, and configure it to log to the account’s S3 bucket.
- D . Confirm in the CloudTrail Console that each trail is active and healthy.
- E . Open the global CloudTrail configuration in the master account, and verify that the storage location is set to the correct S3 bucket.
- F . Confirm in the CloudTrail Console that the S3 bucket name is set correctly.
A company has several workloads running on AWS Employees are required to authenticate using on-premises ADFS and SSO to access the AWS Management Console Developers migrated an existing legacy web application to an Amazon EC2 instance Employees need to access this application from anywhere on the internet but currently, mere is no authentication system but into the application.
How should the Security Engineer implement employee-only access to this system without changing the application?
- A . Place the application behind an Application Load Balancer (ALB) Use Amazon Cognito as authentication (or the ALB Define a SAML-based Amazon Cognito user pool and connect it to ADFS
implement AWS SSO in the master account and link it to ADFS as an identity provide’ Define the EC2 instance as a managed resource, then apply an IAM policy on the resource - B . Define an Amazon Cognito identity pool then install the connector on the Active Directory server Use the Amazon Cognito SDK on the application instance to authenticate the employees using their
- C . Active Directory user names and passwords
- D . Create an AWS Lambda custom authorizer as the authenticator for a reverse proxy on Amazon EC2 Ensure the security group on Amazon EC2 only allows access from the Lambda function.
A company has a website with an Amazon CloudFront HTTPS distribution, an Application Load Balancer (ALB) with multiple web instances for dynamic website content, and an Amazon S3 bucket for static website content.
The company’s security engineer recently updated the website security requirements:
• HTTPS needs to be enforced for all data in transit with specific ciphers.
• The CloudFront distribution needs to be accessible from the internet only.
Which solution will meet these requirements?
Set up an S3 bucket policy with the awssecuretransport key Configure the CloudFront origin access identity (OAI) with the S3 bucket Configure CloudFront to use specific ciphers. Enforce the ALB with an HTTPS listener only and select the appropriate security policy for the ciphers Link the ALB with AWS WAF to allow access from the CloudFront IP ranges.
Set up an S3 bucket policy with the aws:securetransport key. Configure the CloudFront origin access identity (OAI) with the S3 bucket. Enforce the ALB with an HTTPS listener only and select the appropriate security policy for the ciphers.
Modify the CloudFront distribution to use AWS WAF. Force HTTPS on the S3 bucket with specific ciphers in the bucket policy. Configure an HTTPS listener only for the ALB. Set up a security group to limit access to the ALB from the CloudFront IP ranges
Modify the CloudFront distribution to use the ALB as the origin. Enforce an HTTPS listener on the ALB. Create a path-based routing rule on the ALB with proxies that connect lo Amazon S3. Create a bucket policy to allow access from these proxies only.
A company Is trying to replace its on-premises bastion hosts used to access on-premises Linux servers with AWS Systems Manager Session Manager. A security engineer has installed the Systems Manager Agent on all servers. The security engineer verifies that the agent is running on all the servers, but Session Manager cannot connect to them. The security engineer needs to perform verification steps before Session Manager will work on the servers.
Which combination of steps should the security engineer perform? (Select THREE.)
- A . Open inbound port 22 to 0 0.0.0/0 on all Linux servers.
- B . Enable the advanced-instances tier in Systems Manager.
- C . Create a managed-instance activation for the on-premises servers.
- D . Reconfigure the Systems Manager Agent with the activation code and ID.
- E . Assign an IAM role to all of the on-premises servers.
- F . Initiate an inventory collection with Systems Manager on the on-premises servers
A company has recently recovered from a security incident that required the restoration of Amazon EC2 instances from snapshots.
After performing a gap analysis of its disaster recovery procedures and backup strategies, the company is concerned that, next time, it will not be able to recover the EC2 instances if the AWS account was compromised and Amazon EBS snapshots were deleted.
All EBS snapshots are encrypted using an AWS KMS CMK.
Which solution would solve this problem?
- A . Create a new Amazon S3 bucket Use EBS lifecycle policies to move EBS snapshots to
the new S3 bucket. Move snapshots to Amazon S3 Glacier using lifecycle policies, and apply Glacier Vault Lock policies to prevent deletion - B . Use AWS Systems Manager to distribute a configuration that performs local backups of all attached disks to Amazon S3.
- C . Create a new AWS account with limited privileges. Allow the new account to access the AWS KMS key used to encrypt the EBS snapshots, and copy the encrypted snapshots to the new account on a recuning basis
- D . Use AWS Backup to copy EBS snapshots to Amazon S3.
A Security Engineer manages AWS Organizations for a company. The Engineer would like to restrict AWS usage to allow Amazon S3 only in one of the organizational units (OUs).
The Engineer adds the following SCP to the OU:
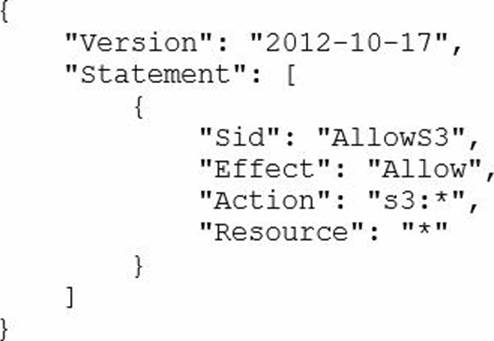
The next day. API calls to AWS IAM appear in AWS CloudTrail logs In an account under that OU.
How should the Security Engineer resolve this issue?
- A . Move the account to a new OU and deny IAM:* permissions.
- B . Add a Deny policy for all non-S3 services at the account level.
- C . Change the policy to:
- D . Detach the default FullAWSAccess SCP
STION NO: 63
A company has a serverless application for internal users deployed on AWS. The application uses AWS Lambda for the front end and for business logic. The Lambda function accesses an Amazon RDS database inside a VPC. The company uses AWS Systems Manager Parameter Store for storing database credentials.
A recent security review highlighted the following issues.
• The Lambda function has internet access.
• The relational database is publicly accessible.
• The database credentials are not stored in an encrypted state.
Which combination of steps should the company take to resolve these security issues? (Select THREE)
- A . Disable public access to the RDS database inside the VPC
- B . Move all the Lambda functions inside the VPC.
- C . Edit the IAM role used by Lambda to restrict internet access.
- D . Create a VPC endpoint for Systems Manager. Store the credentials as a string parameter. Change the parameter type to an advanced parameter.
- E . Edit the IAM role used by RDS to restrict internet access.
- F . Create a VPC endpoint for Systems Manager. Store the credentials as a Secure String parameter.
A company has decided to migrate sensitive documents from on-premises data centers to Amazon S3. Currently, the hard drives are encrypted to meet a compliance requirement regarding data encryption. The CISO wants to improve security by encrypting each file using a different key instead of a single key. Using a different key would limit the security impact of a single exposed key.
Which of the following requires the LEAST amount of configuration when implementing this approach?
- A . Place each file into a different S3 bucket. Set the default encryption of each bucket to use a different AWS KMS customer managed key.
- B . Put all the files in the same S3 bucket. Using S3 events as a trigger, write an AWS Lambda function to encrypt each file as it is added using different AWS KMS data keys.
- C . Use the S3 encryption client to encrypt each file individually using S3-generated data keys
- D . Place all the files in the same S3 bucket. Use server-side encryption with AWS KMS-managed keys (SSE-KMS) to encrypt the data
A company hosts a web-based application that captures and stores sensitive data in an Amazon DynamoDB table. A security audit reveals that the application does not provide end-to-end data protection or the ability to detect unauthorized data changes. The software engineering team needs to make changes that will address the audit findings.
Which set of steps should the software engineering team take?
- A . Use an AWS Key Management Service (AWS KMS) CMK. Encrypt the data at rest.
- B . Use AWS Certificate Manager (ACM) Private Certificate Authority Encrypt the data in transit.
- C . Use a DynamoDB encryption client. Use client-side encryption and sign the table items
- D . Use the AWS Encryption SDK. Use client-side encryption and sign the table items.
A company uses a third-party identity provider and SAML-based SSO for its AWS accounts After the third-party identity provider renewed an expired signing certificate users saw the following message when trying to log in:
A security engineer needs to provide a solution that corrects the error and minimizes operational overhead Which solution meets these requirements?
- A . Upload the third-party signing certificate’s new private key to the AWS identity provider entity defined in AWS identity and Access Management (IAM) by using the AWS Management Console
- B . Sign the identity provider’s metadata file with the new public key Upload the signature to the AWS identity provider entity defined in AWS Identity and Access Management (IAM) by using the AWS CLI.
- C . Download the updated SAML metadata tile from the identity service provider Update the file in the AWS identity provider entity defined in AWS Identity and Access Management (IAM) by using the AWS CLI
- D . Configure the AWS identity provider entity defined in AWS Identity and Access Management (IAM) to synchronously fetch the new public key by using the AWS Management Console.
A company has a compliance requirement to rotate its encryption keys on an annual basis. A Security Engineer needs a process to rotate the KMS Customer Master Keys (CMKs) that were created using imported key material.
How can the Engineer perform the key rotation process MOST efficiently?
- A . Create a new CMK, and redirect the existing Key Alias to the new CMK
- B . Select the option to auto-rotate the key
- C . Upload new key material into the existing CMK.
- D . Create a new CMK, and change the application to point to the new CMK
A company’s Developers plan to migrate their on-premises applications to Amazon EC2 instances running Amazon Linux AMIs. The applications are accessed by a group of partner companies.
The Security Engineer needs to implement the following host-based security measures for these instances:
• Block traffic from documented known bad IP addresses
* Detect known software vulnerabilities and CIS Benchmarks compliance.
Which solution addresses these requirements?
- A . Launch the EC2 instances with an IAM role attached. Include a user data script that uses the AWS CLI to retrieve the list of bad IP addresses from AWS Secrets Manager and uploads it as a threat list in Amazon GuardDuty Use Amazon Inspector to scan the instances for known software vulnerabilities and CIS Benchmarks compliance
- B . Launch the EC2 instances with an IAM role attached Include a user data script that uses the AWS CLl to create NACLs blocking ingress traffic from the known bad IP addresses in the EC2 instance’s subnets Use AWS Systems Manager to scan the instances for known software vulnerabilities, and AWS Trusted Advisor to check instances for CIS Benchmarks compliance
- C . Launch the EC2 instances with an IAM role attached Include a user data script that uses the AWS CLl to create and attach security groups that only allow an allow listed source IP address range inbound. Use Amazon Inspector to scan the instances for known software vulnerabilities, and AWS Trusted Advisor to check instances for CIS Benchmarks compliance
- D . Launch the EC2 instances with an IAM role attached Include a user data script that creates a cron job to periodically retrieve the list of bad IP addresses from Amazon S3, and configures iptabies on the instances blocking the list of bad IP addresses Use Amazon inspector to scan the instances for known software vulnerabilities and CIS Benchmarks compliance.
A Security Engineer noticed an anomaly within a company EC2 instance as shown in the image.
The Engineer must now investigate what e causing the anomaly.
What are the MOST effective steps to take lo ensure that the instance is not further manipulated while allowing the Engineer to understand what happened?
- A . Remove the instance from the Auto Scaling group Place the instance within an isolation security group, detach the EBS volume launch an EC2 instance with a forensic toolkit and attach the E8S volume to investigate
- B . Remove the instance from the Auto Scaling group and the Elastic Load Balancer Place the instance within an isolation security group, launch an EC2 instance with a forensic toolkit, and allow the forensic toolkit image to connect to the suspicious Instance to perform the Investigation.
- C . Remove the instance from the Auto Scaling group Place the Instance within an isolation security group, launch an EC2 Instance with a forensic toolkit and use the forensic toolkit imago to deploy an ENI as a network span port to inspect all traffic coming from the suspicious instance.
- D . Remove the instance from the Auto Scaling group and the Elastic Load Balancer Place the instance within an isolation security group, make a copy of the EBS volume from a new snapshot, launch an EC2 Instance with a forensic toolkit and attach the copy of the EBS volume to investigate.
A security engineer needs to configure monitonng and auditing for AWS Lambda.
Which combination of actions using AWS services should the security engineer take to accomplish this goal? (Select TWO.)
- A . Use AWS Config to track configuration changes to Lambda functions, runtime environments, tags, handler names, code sizes, memory allocation, timeout settings, and concurrency settings, along with Lambda IAM execution role, subnet, and security group associations.
- B . Use AWS CloudTrail to implement governance, compliance, operational, and risk auditing for Lambda.
- C . Use Amazon Inspector to automatically monitor for vulnerabilities and perform governance, compliance, operational, and risk auditing for Lambda.
- D . Use AWS Resource Access Manager to track configuration changes to Lambda functions, runtime environments, tags, handler names, code sizes, memory allocation, timeout settings, and concurrency settings, along with Lambda IAM execution role, subnet, and security group associations.
- E . Use Amazon Macie to discover, classify, and protect sensitive data being executed inside the Lambda function.
A company has an AWS account and allows a third-party contractor who uses another AWS account, to assume certain IAM roles. The company wants to ensure that IAM roles can be assumed by the contractor only if the contractor has multi-factor authentication enabled on their IAM user accounts
What should the company do to accomplish this?
A)
B)
C)
D)
- A . Option A
- B . Option B
- C . Option C
- D . Option D
A company uses Microsoft Active Directory for access management for on-premises resources and wants to use the same mechanism for accessing its AWS accounts. Additionally, the development team plans to launch a public-facing application for which they need a separate authentication solution.
When coma nation of the following would satisfy these requirements? (Select TWO)
- A . Set up domain controllers on Amazon EC2 to extend the on-premises directory to AWS
- B . Establish network connectivity between on-premises and the user’s VPC
- C . Use Amazon Cognito user pools for application authentication
- D . Use AD Connector tor application authentication.
- E . Set up federated sign-in to AWS through ADFS and SAML.
A company wants to encrypt data locally while meeting regulatory requirements related to key exhaustion. The encryption key can be no more than 10 days old or encrypt more than 2" 16 objects Any encryption key must be generated on a FlPS-validated hardware security module (HSM). The company is cost-conscious, as plans to upload an average of 100 objects to Amazon S3 each second for sustained operations across 5 data producers
When approach MOST efficiently meets the company’s needs?
- A . Use the AWS Encryption SDK and set the maximum age to 10 days and the minimum number of messages encrypted to 3" 16. Use AWS Key Management Service (AWS KMS) to generate the master key and data key Use data key caching with the Encryption SDk during the encryption process.
- B . Use AWS Key Management Service (AWS KMS) to generate an AWS managed CMK. Then use Amazon S3 client-side encryption configured to automatically rotate with every object
- C . Use AWS CloudHSM to generate the master key and data keys. Then use Boto 3 and
Python to locally encrypt data before uploading the object Rotate the data key every 10 days or after 2" 16 objects have been Uploaded to Amazon 33 - D . Use server-side encryption with Amazon S3 managed encryption keys (SSE-S3) and set the master key to automatically rotate.
A company plans to use custom AMIs to launch Amazon EC2 instances across multiple AWS accounts in a single Region to perform security monitoring and analytics tasks. The EC2 instances are launched in EC2 Auto Scaling groups. To increase the security of the solution, a Security Engineer will manage the lifecycle of the custom AMIs in a centralized account and will encrypt them with a centrally managed AWS KMS CMK. The Security Engineer configured the KMS key policy to allow cross-account access. However, the EC2 instances are still not being properly launched by the EC2 Auto Scaling groups.
Which combination of configuration steps should the Security Engineer take to ensure the EC2 Auto Scaling groups have been granted the proper permissions to execute tasks?
- A . Create a customer-managed CMK in the centralized account. Allow other applicable accounts to use that key for cryptographical operations by applying proper cross-account permissions in the key policy. Create an IAM role in all applicable accounts and configure its access policy to allow the use of the centrally managed CMK for cryptographical operations. Configure EC2 Auto Scaling groups within each applicable account to use the created IAM role to launch EC2 instances.
- B . Create a customer-managed CMK in the centralized account. Allow other applicable accounts to use that key for cryptographical operations by applying proper cross-account permissions in the key policy. Create an IAM role in all applicable accounts and configure its access policy with permissions to create grants for the centrally managed CMK. Use this IAM role to create a grant for the centrally managed CMK with permissions to perform cryptographical operations and with the EC2 Auto Scaling service-linked role defined as the grantee principal.
- C . Create a customer-managed CMK or an AWS managed CMK in the centralized account. Allow other applicable accounts to use that key for cryptographical operations by applying proper cross-account permissions in the key policy. Use the CMK administrator to create a CMK grant that includes permissions to perform cryptographical operations that define EC2 Auto Scaling service-linked roles from all other accounts as the grantee principal.
- D . Create a customer-managed CMK or an AWS managed CMK in the centralized account. Allow other applicable accounts to use that key for cryptographical operations by applying proper cross-account permissions in the key policy. Modify the access policy for the EC2 Auto Scaling roles to perform cryptographical operations against the centrally managed CMK.
A security engineer is designing a solution that will provide end-to-end encryption between clients and Docker containers running In Amazon Elastic Container Service (Amazon ECS). This solution will also handle volatile traffic patterns.
Which solution would have the MOST scalability and LOWEST latency?
- A . Configure a Network Load Balancer to terminate the TLS traffic and then re-encrypt the traffic to the containers
- B . Configure an Application Load Balancer to terminate the TLS traffic and then re-encrypt the traffic to the containers
- C . Configure a Network Load Balancer with a TCP listener to pass through TLS traffic to the containers
- D . Configure Amazon Route 53 to use multivalue answer routing to send traffic to the containers
A security engineer has noticed an unusually high amount of traffic coming from a single IP address. This was discovered by analyzing the Application Load Balancer’s access logs.
How can the security engineer limit the number of requests from a specific IP address without blocking the IP address?
- A . Add a rule to the Application Load Balancer to route the traffic originating from the IP address in question and show a static webpage.
- B . Implement a rate-based rule with AWS WAF
- C . Use AWS Shield to limit the originating traffic hit rate.
- D . Implement the GeoLocation feature in Amazon Route 53.
A Security Engineer has several thousand Amazon EC2 instances split across production and development environments. Each instance is tagged with its environment. The Engineer needs to analyze and patch all the development EC2 instances to ensure they are not currently exposed to any common vulnerabilities or exposures (CVEs).
Which combination of steps is the MOST efficient way for the Engineer to meet these requirements? (Select TWO.)
- A . Log on to each EC2 instance, check and export the different software versions installed, and verify this against a list of current CVEs.
- B . Install the Amazon Inspector agent on all development instances Build a custom rule package, and configure Inspector to perform a scan using this custom rule on all instances tagged as being in the development environment.
- C . Install the Amazon Inspector agent on all development instances Configure Inspector to perform a scan using the CVE rule package on all instances tagged as being in the development environment.
- D . Install the Amazon EC2 System Manager agent on all development instances Issue the Run command to EC2 System Manager to update all instances
- E . Use AWS Trusted Advisor to check that all EC2 instances have been patched to the most recent version of operating system and installed software.
An application running on Amazon EC2 instances generates log files in a folder on a Linux file system. The instances block access to the console and file transfer utilities, such as Secure Copy Protocol (SCP) and Secure File Transfer Protocol (SFTP). The Application Support team wants to automatically monitor the application log files so the team can set up notifications in the future.
A Security Engineer must design a solution that meets the following requirements:
• Make the log files available through an AWS managed service.
• Allow for automatic monitoring of the logs.
• Provide an Interlace for analyzing logs.
• Minimize effort.
Which approach meets these requirements^
- A . Modify the application to use the AWS SDK Write the application logs lo an Amazon S3 bucket
- B . install the unified Amazon CloudWatch agent on the instances Configure the agent to
collect the application log dies on the EC2 tile system and send them to Amazon CloudWatch Logs - C . Install AWS Systems Manager Agent on the instances Configure an automation document to copy the application log files to AWS DeepLens
- D . Install Amazon Kinesis Agent on the instances Stream the application log files to Amazon Kinesis Data Firehose and sot the destination to Amazon Elasticsearch Service
To meet regulatory requirements, a Security Engineer needs to implement an IAM policy that restricts the use of AWS services to the us-east-1 Region.
What policy should the Engineer implement?
A)
B)
C)
D)
- A . Option A
- B . Option B
- C . Option C
- D . Option D
A company has a VPC with an IPv6 address range and a public subnet with an IPv6 address block. The VPC currently hosts some public Amazon EC2 instances but a Security Engineer needs to migrate a second application into the VPC that also requires IPv6 connectivity.
This new application will occasionally make API requests to an external, internet-accessible endpoint to receive updates However, the Security team does not want the application’s EC2 instance exposed directly to the internet The Security Engineer intends to create a private subnet with a custom route table and to associate the route table with the private subnet
What else does the Security Engineer need to do to ensure the application will not be exposed directly to the internet, but can still communicate as required”
- A . Launch a NAT instance in the public subnet Update the custom route table with a new
route to the NAT instance - B . Remove the internet gateway, and add AWS PrivateLink to the VPC Then update the custom route table with a new route to AWS PrivateLink
- C . Add a managed NAT gateway to the VPC Update the custom route table with a new route to the gateway
- D . Add an egress-only internet gateway to the VPC. Update the custom route table with a new route to the gateway
A Security Engineer accidentally deleted the imported key material in an AWS KMS CMK.
What should the Security Engineer do to restore the deleted key material?
- A . Create a new CMK. Download a new wrapping key and a new import token to import the original key material
- B . Create a new CMK Use the original wrapping key and import token to import the original key material.
- C . Download a new wrapping key and a new import token Import the original key material into the existing CMK.
- D . Use the original wrapping key and import token Import the original key material into the existing CMK
Authorized Administrators are unable to connect to an Amazon EC2 Linux bastion host using SSH over the internet. The connection either fails to respond or generates the following error message:
Network error: Connection timed out.
What could be responsible for the connection failure? (Select THREE)
- A . The NAT gateway in the subnet where the EC2 instance is deployed has been misconfigured
- B . The internet gateway of the VPC has been reconfigured
- C . The security group denies outbound traffic on ephemeral ports
- D . The route table is missing a route to the internet gateway
- E . The NACL denies outbound traffic on ephemeral ports
- F . The host-based firewall is denying SSH traffic
A company is setting up products to deploy in AWS Service Catalog. Management is concerned that when users launch products, elevated IAM privileges will be required to create resources.
How should the company mitigate this concern?
- A . Add a template constraint to each product in the portfolio.
- B . Add a launch constraint to each product in the portfolio.
- C . Define resource update constraints for each product in the portfolio.
- D . Update the AWS CloudFormalion template backing the product to include a service role configuration.
A company is configuring three Amazon EC2 instances with each instance in a separate Availability Zone. The EC2 instances wilt be used as transparent proxies for outbound internet traffic for ports 80 and 443 so the proxies can block traffic to certain internet destinations as required by the company’s security policies.
A Security Engineer completed the following:
• Set up the proxy software on the EC2 instances.
• Modified the route tables on the private subnets to use the proxy EC2 instances as the default route.
• Created a security group rule opening inbound port 80 and 443 TCP protocols on the proxy EC2 instance security group.
However, the proxy EC2 instances are not successfully forwarding traffic to the internet.
What should the Security Engineer do to make the proxy EC2 instances route traffic to the internet?
- A . Put all the proxy EC2 instances in a cluster placement group.
- B . Disable source and destination checks on the proxy EC2 instances.
- C . Open all inbound ports on the proxy EC2 instance security group.
- D . Change the VPC’s DHCP domain-name-servers options set to the IP addresses of proxy EC2 instances.
A financial institution has the following security requirements:
• Cloud-based users must be contained in a separate authentication domain.
• Cloud-based users cannot access on-premises systems.
As part of standing up a cloud environment, the financial institution is creating a number of Amazon managed databases and Amazon EC2 instances. An Active Directory service exists on-premises that has all the administrator accounts, and these must be able to access the databases and instances.
How would the organization manage its resources in the MOST secure manner? (Choose two.)
- A . Configure an AWS Managed Microsoft AD to manage the cloud resources.
- B . Configure an additional on-premises Active Directory service to manage the cloud resources.
- C . Establish a one-way trust relationship from the existing Active Directory to the new Active Directory service.
- D . Establish a one-way trust relationship from the new Active Directory to the existing Active Directory service.
- E . Establish a two-way trust between the new and existing Active Directory services.
A,E
Explanation:
Deploy a new forest/domain on AWS with one-way trust. If you are planning on leveraging credentials from an on-premises AD on AWS member servers, you must establish at least a one-way trust to the Active Directory running on AWS. In this model, the AWS domain becomes the resource domain where computer objects are located and on-premises domain becomes the account domain.
Ref: https://d1.awsstatic.com/whitepapers/adds-on-aws.pdf
An application developer is using an AWS Lambda function that must use AWS KMS to perform encrypt and decrypt operations for API keys that are less than 2 KB.
Which key policy would allow the application to do this while granting least privilege?
- A . Option A
- B . Option B
- C . Option C
- D . Option D
A Developer is building a serverless application that uses Amazon API Gateway as the front end. The application will not be publicly accessible. Other legacy applications running on Amazon EC2 will make calls to the application A Security Engineer Has been asked to review the security controls for authentication and authorization of the application.
Which combination of actions would provide the MOST secure solution? (Select TWO)
- A . Configure an IAM policy that allows the least permissive actions to communicate with the API Gateway Attach the policy to the role used by the legacy EC2 instances
- B . Enable AWS WAF for API Gateway Configure rules to explicitly allow connections from the legacy EC2 instances
- C . Create a VPC endpoint for API Gateway Attach an IAM resource policy that allows the role of the legacy EC2 instances to call specific APIs
- D . Create a usage plan Generate a set of API keys for each application that needs to call the API.
- E . Configure cross-origin resource sharing (CORS) in each API Share the CORS information with the applications that call the API.
A company has an encrypted Amazon S3 bucket. An Application Developer has an IAM policy that allows access to the S3 bucket, but the Application Developer is unable to access objects within the bucket.
What is a possible cause of the issue?
- A . The S3 ACL for the S3 bucket fails to explicitly grant access to the Application Developer
- B . The AWS KMS key for the S3 bucket fails to list the Application Developer as an administrator
- C . The S3 bucket policy fails to explicitly grant access to the Application Developer
- D . The S3 bucket policy explicitly denies access to the Application Developer
A company’s web application is hosted on Amazon EC2 instances running behind an Application Load Balancer (ALB) in an Auto Scaling group. An AWS WAF web ACL is associated with the ALB. AWS CloudTrail is enabled, and stores logs in Amazon S3 and Amazon CloudWatch Logs.
The operations team has observed some EC2 instances reboot at random. After rebooting, all access logs on the instances have been deleted. During an investigation, the operations team found that each reboot happened just after a PHP error occurred on the new-user-creation.php file. The operations team needs to view log information to determine if the company is being attacked.
Which set of actions will identify the suspect attacker’s IP address for future occurrences?
- A . Configure VPC Flow Logs on the subnet where the ALB is located, and stream the data CloudWatch. Search for the new-user-creation.php occurrences in CloudWatch.
- B . Configure the CloudWatch agent on the ALB Configure the agent to send application logs to CloudWatch Update the instance role to allow CloudWatch Logs access. Export the logs to CloudWatch Search for the new-user-creation.php occurrences in CloudWatch.
- C . Configure the ALB to export access logs to an Amazon Elasticsearch Service cluster, and use the service to search for the new-user-creation.php occurrences.
- D . Configure the web ACL to send logs to Amazon Kinesis Data Firehose, which delivers the logs to an S3 bucket Use Amazon Athena to query the logs and find the new-user-creation php occurrences.
After a recent security audit involving Amazon S3, a company has asked assistance reviewing its S3 buckets to determine whether data is properly secured.
The first S3 bucket on the list has the following bucket policy.
Is this bucket policy sufficient to ensure that the data is not publicity accessible?
- A . Yes, the bucket policy makes the whole bucket publicly accessible despite now the S3 bucket ACL or object ACLs are configured.
- B . Yes, none of the data in the bucket is publicity accessible, regardless of how the S3 bucket ACL and object ACLs are configured.
- C . No, the IAM user policy would need to be examined first to determine whether any data is publicly accessible.
- D . No, the S3 bucket ACL and object ACLs need to be examined first to determine whether any data is publicly accessible.
A company’s security engineer is configuring Amazon S3 permissions to ban all current and future public buckets However, the company hosts several websites directly off S3 buckets with public access enabled. The engineer needs to bock me pubic S3 buckets without causing any outages on me easting websites. The engineer has set up an Amazon CloudFrom distribution (or each website.
Which set or steps should the security engineer implement next?
- A . Configure an S3 bucket as the origin an origin access identity (OAI) for the CloudFront distribution Switch the DNS records from websites to point to the CloudFront distribution Enable Nock public access settings at the account level
- B . Configure an S3 bucket as the origin with an origin access identity (OAI) for the CloudFront distribution Switch the ONS records tor the websites to point to the CloudFront disinfection Then, tor each S3 bucket enable block public access settings
- C . Configure an S3 bucket as the origin with an origin access identity (OAI) for the CloudFront distribution Enable block public access settings at the account level
- D . Configure an S3 bucket as the origin for me CloudFront distribution Configure the S3 bucket policy to accept connections from the CloudFront points of presence only Switch the DNS records for the websites to point to the CloudFront distribution Enable block public access settings at me account level
An application is currently secured using network access control lists and security groups. Web servers are located in public subnets behind an Application Load Balancer (ALB); application servers are located in private subnets.
How can edge security be enhanced to safeguard the Amazon EC2 instances against attack? (Choose two.)
- A . Configure the application’s EC2 instances to use NAT gateways for all inbound traffic.
- B . Move the web servers to private subnets without public IP addresses.
- C . Configure AWS WAF to provide DDoS attack protection for the ALB.
- D . Require all inbound network traffic to route through a bastion host in the private subnet.
- E . Require all inbound and outbound network traffic to route through an AWS Direct Connect connection.
A company wants to encrypt the private network between its orvpremises environment and AWS. The company also wants a consistent network experience for its employees.
What should the company do to meet these requirements?
- A . Establish an AWS Direct Connect connection with AWS and set up a Direct Connect gateway. In the Direct Connect gateway configuration, enable IPsec and BGP, and then leverage native AWS network encryption between Availability Zones and Regions,
- B . Establish an AWS Direct Connect connection with AWS and set up a Direct Connect gateway. Using the Direct Connect gateway, create a private virtual interface and advertise the customer gateway private IP addresses. Create a VPN connection using the customer gateway and the virtual private gateway
- C . Establish a VPN connection with the AWS virtual private cloud over the internet
- D . Establish an AWS Direct Connect connection with AWS and establish a public virtual interface. For prefixes that need to be advertised, enter the customer gateway public IP addresses. Create a VPN connection over Direct Connect using the customer gateway and the virtual private gateway.
A company has decided to use encryption in its AWS account to secure the objects in Amazon S3 using server-side encryption. Object sizes range from 16.000 B to 5 MB.
The requirements are as follows:
• The key material must be generated and stored in a certified Federal Information Processing Standard (FIPS) 140-2 Level 3 machine.
• The key material must be available in multiple Regions.
Which option meets these requirements?
- A . Use an AWS KMS customer managed key and store the key material in AWS with replication across Regions
- B . Use an AWS customer managed key, import the key material into AWS KMS using in-house AWS CloudHSM. and store the key material securely in Amazon S3.
- C . Use an AWS KMS custom key store backed by AWS CloudHSM clusters, and copy backups across Regions
- D . Use AWS CloudHSM to generate the key material and backup keys across Regions Use the Java Cryptography Extension (JCE) and Public Key Cryptography Standards #11 (PKCS #11) encryption libraries to encrypt and decrypt the data.
A global company that deals with International finance is investing heavily in cryptocurrencies and wants to experiment with mining technologies using AWS. The company’s security team has enabled Amazon GuardDuty and is concerned by the number of findings being generated by the accounts. The security team wants to minimize the possibility of GuardDuty finding false negatives for compromised instances that are performing mining
How can the security team continue using GuardDuty while meeting these requirements?
- A . In the GuardDuty console, select the CryptoCurrency:EC2/BitcoinTool B’DNS finding and use the suppress findings option
- B . Create a custom AWS Lambda function to process newly detected GuardDuty alerts Process the CryptoCurrency EC2/BitcoinTool BIDNS alert and filter out the high-severity finding types only.
- C . When creating a new Amazon EC2 Instance, provide the instance with a specific tag that indicates it is performing mining operations Create a custom AWS Lambda function to process newly detected GuardDuty alerts and filter for the presence of this tag
- D . When GuardDuty produces a cryptocurrency finding, process the finding with a custom AWS Lambda function to extract the instance ID from the finding Then use the AWS Systems Manager Run Command to check for a running process performing mining operations
A security engineer must use AWS Key Management Service (AWS KMS) to design a key management solution for a set of Amazon Elastic Block Store (Amazon EBS) volumes that contain sensitive data. The solution needs to ensure that the key material automatically expires in 90 days.
Which solution meets these criteria?
- A . A customer managed CMK that uses customer provided key material
- B . A customer managed CMK that uses AWS provided key material
- C . An AWS managed CMK
- D . Operating system-native encryption that uses GnuPG
A company’s application runs on Amazon EC2 and stores data in an Amazon S3 bucket The company wants additional security controls in place to limit the likelihood of accidental exposure of data to external parties.
Which combination of actions will meet this requirement? (Select THREE.)
- A . Encrypt the data in Amazon S3 using server-side encryption with Amazon S3 managed encryption keys (SSE-S3)
- B . Encrypt the data in Amazon S3 using server-side encryption with AWS KMS managed encryption keys (SSE-KMS)
- C . Create a new Amazon S3 VPC endpoint and modify the VPC’s routing tables to use the new endpoint
- D . Use the Amazon S3 Block Public Access feature.
- E . Configure the bucket policy to allow access from the application instances only
- F . Use a NACL to filter traffic to Amazon S3
A Security Administrator at a university is configuring a fleet of Amazon EC2 instances. The EC2 instances are shared among students, and non-root SSH access is allowed. The Administrator is concerned about students attacking other AWS account resources by using the EC2 instance metadata service.
What can the Administrator do to protect against this potential attack?
- A . Disable the EC2 instance metadata service.
- B . Log all student SSH interactive session activity.
- C . Implement ip tables-based restrictions on the instances.
- D . Install the Amazon Inspector agent on the instances.
A
Explanation:
"To turn off access to instance metadata on an existing instance….."
https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/configuring-instance-metadata-service.html You can disable the service for existing (running or stopped) ec2 instances.
https://docs.aws.amazon.com/cli/latest/reference/ec2/modify-instance-metadata-options.html
An employee accidentally exposed an AWS access key and secret access key during a public presentation. The company Security Engineer immediately disabled the key.
How can the Engineer assess the impact of the key exposure and ensure that the credentials were not misused? (Choose two.)
- A . Analyze AWS CloudTrail for activity.
- B . Analyze Amazon CloudWatch Logs for activity.
- C . Download and analyze the IAM Use report from AWS Trusted Advisor.
- D . Analyze the resource inventory in AWS Config for IAM user activity.
- E . Download and analyze a credential report from IAM.
A,E
Explanation:
https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_getting-report.html
A company has several production AWS accounts and a central security AWS account. The security account is used for centralized monitoring and has IAM privileges to all resources in every corporate account. All of the company’s Amazon S3 buckets are tagged with a value denoting the data classification of their contents.
A Security Engineer is deploying a monitoring solution in the security account that will enforce bucket policy compliance. The system must monitor S3 buckets in all production accounts and confirm that any policy change is in accordance with the bucket’s data classification. If any change is out of compliance; the Security team must be notified quickly.
Which combination of actions would build the required solution? (Choose three.)
- A . Configure Amazon CloudWatch Events in the production accounts to send all S3 events to the security account event bus.
- B . Enable Amazon GuardDuty in the security account. and join the production accounts as members.
- C . Configure an Amazon CloudWatch Events rule in the security account to detect S3 bucket creation or modification events.
- D . Enable AWS Trusted Advisor and activate email notifications for an email address assigned to the security contact.
- E . Invoke an AWS Lambda function in the security account to analyze S3 bucket settings in response to S3 events, and send non-compliance notifications to the Security team.
- F . Configure event notifications on S3 buckets for PUT; POST, and DELETE events.
A security engineer is auditing a production system and discovers several additional IAM roles that are not required and were not previously documented during the last audit 90 days ago. The engineer is trying to find out who created these IAM roles and when they were created. The solution must have the lowest operational overhead.
Which solution will meet this requirement?
- A . Import AWS CloudTrail logs from Amazon S3 into an Amazon Elasticsearch Service cluster, and search through the combined logs for CreateRole events.
- B . Create a table in Amazon Athena for AWS CloudTrail events. Query the table in Amazon Athena for CreateRole events.
- C . Use AWS Config to look up the configuration timeline for the additional IAM roles and view the linked AWS CloudTrail event.
- D . Download the credentials report from the IAM console to view the details for each IAM entity, including the creation dates.
After multiple compromises of its Amazon EC2 instances, a company’s Security Officer is mandating that memory dumps of compromised instances be captured for further analysis. A Security Engineer just received an EC2 abuse notification report from AWS stating that an EC2 instance running the most recent Windows Server 2019 Base AMI is compromised.
How should the Security Engineer collect a memory dump of the EC2 instance for forensic analysis?
- A . Give consent to the AWS Security team to dump the memory core on the compromised instance and provide it to AWS Support for analysis.
- B . Review memory dump data that the AWS Systems Manager Agent sent to Amazon CloudWatch Logs.
- C . Download and run the EC2Rescue for Windows Server utility from AWS.
- D . Reboot the EC2 Windows Server, enter safe mode, and select memory dump.
A Security Engineer creates an Amazon S3 bucket policy that denies access to all users. A few days later, the Security Engineer adds an additional statement to the bucket policy to allow read-only access to one other employee Even after updating the policy the employee still receives an access denied message.
What is the likely cause of this access denial?
- A . The ACL in the bucket needs to be updated.
- B . The IAM policy does not allow the user to access the bucket
- C . It takes a few minutes for a bucket policy to take effect
- D . The allow permission is being overridden by the deny.
A security engineer must develop an encryption tool for a company. The company requires a cryptographic solution that supports the ability to perform cryptographic erasure on all resources protected by the key material in 15 minutes or less
Which AWS Key Management Service (AWS KMS) key solution will allow the security engineer to meet these requirements?
- A . Use Imported key material with CMK
- B . Use an AWS KMS CMK
- C . Use an AWS managed CMK.
- D . Use an AWS KMS customer managed CMK
A company is using AWS Organizations to manage multiple AWS member accounts. All of these accounts have Amazon GuardDuty enabled in all Regions. The company’s AW5 Security Operations Center has a centralized security account for logging and monitoring. One of the member accounts has received an excessively high bill A security engineer discovers that a compromised Amazon EC2 instance is being used to mine crypto currency. The Security Operations Center did not receive a GuardDuty finding in the central security account.
but there was a GuardDuty finding in the account containing the compromised EC2 instance. The security engineer needs to ensure an GuardDuty finding are available in the security account.
What should the security engineer do to resolve this issue?
- A . Set up an Amazon CloudWatch Event rule to forward ail GuardDuty findings to the security account Use an AWS Lambda function as a target to raise findings
- B . Set up an Amazon CloudWatch Events rule to forward all GuardDuty findings to the security account Use an AWS Lambda function as a target to raise findings in AWS Security Hub
- C . Check that GuardDuty in the security account is able to assume a role in the compromised account using the GuardDuty fast findings permission Schedule an Amazon CloudWatch Events rule and an AWS Lambda function to periodically check for GuardDuty findings
- D . Use the aws GuardDuty get-members AWS CLI command m the security account to see if the account is listed Send an invitation from GuardDuty m the security account to GuardDuty in the compromised account Accept the invitation to forward all future GuardDuty findings
An external Auditor finds that a company’s user passwords have no minimum length.
The company is currently using two identity providers:
• AWS IAM federated with on-premises Active Directory
• Amazon Cognito user pools to accessing an AWS Cloud application developed by the company
Which combination o1 actions should the Security Engineer take to solve this issue? (Select TWO.)
- A . Update the password length policy In the on-premises Active Directory configuration.
- B . Update the password length policy In the IAM configuration.
- C . Enforce an IAM policy In Amazon Cognito and AWS IAM with a minimum password length condition.
- D . Update the password length policy in the Amazon Cognito configuration.
- E . Create an SCP with AWS Organizations that enforces a minimum password length for AWS IAM and Amazon Cognito.
A Developer signed in to a new account within an AWS Organizations organizations unit (OU) containing multiple accounts.
Access to the Amazon S3 service is restricted with the following SCP:
How can the Security Engineer provide the Developer with Amazon S3 access without affecting other accounts?
- A . Move the SCP to the root OU of Organizations to remove the restriction to access Amazon S3.
- B . Add an IAM policy for the Developer, which grants S3 access.
- C . Create a new OU without applying the SCP restricting S3 access. Move the Developer account to this new OU.
- D . Add an allow list for the Developer account for the S3 service.
A company’s development team is designing an application using AWS Lambda and Amazon Elastic Container Service (Amazon ECS). The development team needs to create IAM roles to support these systems. The company’s security team wants to allow the developers to build IAM roles directly, but the security team wants to retain control over the permissions the developers can delegate to those roles. The development team needs access to more permissions than those required for the application’s AWS services. The solution must minimize management overhead.
How should the security team prevent privilege escalation for both teams?
- A . Enable AWS CloudTrail. Create a Lambda function that monitors the event history for privilege escalation events and notifies the security team.
- B . Create a managed IAM policy for the permissions required. Reference the IAM policy as a permissions boundary within the development team’s IAM role.
- C . Enable AWS Organizations Create an SCP that allows the IAM CreateUser action but that has a condition that prevents API calls other than those required by the development team
- D . Create an IAM policy with a deny on the IAMCreateUser action and assign the policy to the development team. Use a ticket system to allow the developers to request new IAM roles for their applications. The IAM roles will then be created by the security team.
A company had one of its Amazon EC2 key pairs compromised. A Security Engineer must identify which current Linux EC2 instances were deployed and used the compromised key pair.
How can this task be accomplished?
- A . Obtain the list of instances by directly querying Amazon EC2 using: aws ec2 describe-instances –fi1ters "Name=key-name,Values=KEYNAMEHERE".
- B . Obtain the fingerprint for the key pair from the AWS Management Console, then search for the fingerprint in the Amazon Inspector logs.
- C . Obtain the output from the EC2 instance metadata using: curl http: //169.254.169.254/latest/meta-data/public- keys/0/.
- D . Obtain the fingerprint for the key pair from the AWS Management Console, then search for the fingerprint in Amazon CloudWatch Logs using: aws logs filter-log-events.
A Developer reported that AWS CloudTrail was disabled on their account. A Security Engineer investigated the account and discovered the event was undetected by the current security solution. The Security Engineer must recommend a solution that will detect future changes to the CloudTrail configuration and send alerts when changes occur.
What should the Security Engineer do to meet these requirements?
- A . Use AWS Resource Access Manager (AWS RAM) to monitor the AWS CloudTrail configuration. Send notifications using Amazon SNS.
- B . Create an Amazon CloudWatch Events rule to monitor Amazon GuardDuty findings.
Send email notifications using Amazon SNS. - C . Update security contact details in AWS account settings for AWS Support to send alerts when suspicious activity is detected.
- D . Use Amazon Inspector to automatically detect security issues. Send alerts using Amazon SNS.
A security engineer need to ensure their company’s uses of AWS meets AWS security best practices. As part of this, the AWS account root user must not be used for daily work. The root user must be monitored for use, and the Security team must be alerted as quickly as possible if the root user is used.
Which solution meets these requirements?
- A . Set up an Amazon CloudWatch Events rule that triggers an Amazon SNS notification.
- B . Set up an Amazon CloudWatch Events rule that triggers an Amazon SNS notification logs from S3 and generate notifications using Amazon SNS.
- C . Set up a rule in AWS config to trigger root user events. Trigger an AWS Lambda function and generate notifications using Amazon SNS.
- D . Use Amazon Inspector to monitor the usage of the root user and generate notifications using Amazon SNS
A website currently runs on Amazon EC2 with mostly static content on the site. Recently, the site was subjected to a ODoS attack, and a Security Engineer was tasked with redesigning the edge security to help mitigate this risk in the future
What are some ways the Engineer could achieve this? (Select THREE)
- A . Use AWS X-Ray to inspect the traffic going 10 the EC2 instances
- B . Move the state content to Amazon S3 and font this with an Amazon CloudFront distribution
- C . Change the security group configuration to block the source of the attack traffic
- D . Use AWS WAF security rules to inspect the inbound traffic
- E . Use Amazon inspector assessment templates to inspect the inbound traffic
- F . Use Amazon Route 53 to distribute traffic
A company always needs its Amazon Elastic Block Store (Amazon EBS) volumes to be encrypted During a security incident. EBS snapshots of suspicious instances are shared to a forensics account for analysis A security engineer attempting to share a suspicious EBS snapshot to the forensics account receives the following error "Unable to share snapshot: An error occurred (OperationNotPermitted) when calling the ModifySnapshotAttribute operation: Encrypted snapshots with EBS default key cannot be shared.
Which combination of steps should the security engineer take in the incident account to complete the sharing operation? (Select THREE)
- A . Create a customer managed CMK Copy the EBS snapshot encrypting the destination snapshot using the new CMK.
- B . Allow forensics accounting principals to use the CMK by modifying its policy.
- C . Create an Amazon EC2 instance. Attach the encrypted and suspicious EBS volume. Copy data from the suspicious volume to an unencrypted volume. Snapshot the unencrypted volume
- D . Copy the EBS snapshot to the new decrypted snapshot
- E . Restore a volume from the suspicious EBS snapshot. Create an unencrypted EBS volume of the same size.
- F . Share the target EBS snapshot with the forensics account.
A Security Engineer has launched multiple Amazon EC2 instances from a private AMI using an AWS CloudFormation template. The Engineer notices instances terminating right after they are launched.
What could be causing these terminations?
- A . The IAM user launching those instances is missing ec2:Runinstances permission.
- B . The AMI used as encrypted and the IAM does not have the required AWS KMS permissions.
- C . The instance profile used with the EC2 instances in unable to query instance metadata.
- D . AWS currently does not have sufficient capacity in the Region.
A Security Engineer has discovered that, although encryption was enabled on the Amazon S3 bucket example bucket, anyone who has access to the bucket has the ability to retrieve the files. The Engineer wants to limit access to each IAM user can access an assigned folder only.
What should the Security Engineer do to achieve this?
- A . Use envelope encryption with the AWS-managed CMK aws/s3.
- B . Create a customer-managed CMK with a key policy granting “kms:Decrypt” based on the “${aws:username}” variable.
- C . Create a customer-managed CMK for each user. Add each user as a key user in their corresponding key policy.
- D . Change the applicable IAM policy to grant S3 access to “Resource”: “arn:aws:s3:::examplebucket/${aws:username}/*”
B
Reference: https://aws.amazon.com/premiumsupport/knowledge-center/iam-s3-user-specific-folder/
Users report intermittent availability of a web application hosted on AWS. Monitoring systems report an excess of abnormal network traffic followed by high CPU utilization on the application web tier.
Which of the following techniques will improve the availability of the application? (Select TWO.)
- A . Deploy AWS WAF to block all unsecured web applications from accessing the internet.
- B . Deploy an Intrusion Detection/Prevention System (IDS/IPS) to monitor or block unusual incoming network traffic.
- C . Configure security groups to allow outgoing network traffic only from hosts that are protected with up-to-date antivirus software.
- D . Create Amazon CloudFront distribution and configure AWS WAF rules to protect the web applications from malicious traffic.
- E . Use the default Amazon VPC for externakfacing systems to allow AWS to actively block malicious network traffic affecting Amazon EC2 instances.
An AWS account administrator created an IAM group and applied the following managed policy to require that each individual user authenticate using multi-factor authentication:
After implementing the policy, the administrator receives reports that users are unable to perform Amazon EC2 commands using the AWS CLI.
What should the administrator do to resolve this problem while still enforcing multi-factor authentication?
- A . Change the value of aws MultiFactorAuthPresent to true.
- B . Instruct users to run the aws sts get-session-token CLI command and pass the multi-factor authentication ―serial-number and ―token-code parameters. Use these resulting values to make API/CLI calls
- C . Implement federated API/CLI access using SAML 2.0, then configure the identity provider to enforce multi-factor authentication.
- D . Create a role and enforce multi-factor authentication in the role trust policy Instruct users to run the sts assume-role CLI command and pass –serial-number and ―token-code parameters Store the resulting values in environment variables. Add sts:AssumeRole to NotAction in the policy.
The Security Engineer is managing a traditional three-tier web application that is running on Amazon EC2 instances. The application has become the target of increasing numbers of malicious attacks from the Internet.
What steps should the Security Engineer take to check for known vulnerabilities and limit the attack surface? (Choose two.)
- A . Use AWS Certificate Manager to encrypt all traffic between the client and application servers.
- B . Review the application security groups to ensure that only the necessary ports are open.
- C . Use Elastic Load Balancing to offload Secure Sockets Layer encryption.
- D . Use Amazon Inspector to periodically scan the backend instances.
- E . Use AWS Key Management Services to encrypt all the traffic between the client and application servers.
A Security Engineer discovered a vulnerability in an application running on Amazon ECS. The vulnerability allowed attackers to install malicious code. Analysis of the code shows it exfiltrates data on port 5353 in batches at random time intervals.
While the code of the containers is being patched, how can Engineers quickly identify all compromised hosts and stop the egress of data on port 5353?
- A . Enable AWS Shield Advanced and AWS WAF. Configure an AWS WAF custom filter for egress traffic on port 5353
- B . Enable Amazon Inspector on Amazon ECS and configure a custom assessment to evaluate containers that have port 5353 open. Update the NACLs to block port 5353 outbound.
- C . Create an Amazon CloudWatch custom metric on the VPC Flow Logs identifying egress traffic on port 5353. Update the NACLs to block port 5353 outbound.
- D . Use Amazon Athena to query AWS CloudTrail logs in Amazon S3 and look for any traffic on port 5353. Update the security groups to block port 5353 outbound.
A company’s Director of information Security wants a daily email report from AWS that contains recommendations for each company account to meet AWS Security best practices.
Which solution would meet these requirements?
- A . in every AWS account, configure AWS Lambda to query me AWS Support API tor AWS Trusted Advisor security checks Send the results from Lambda to an Amazon SNS topic to send reports.
- B . Configure Amazon GuardDuty in a master account and invite all other accounts to be managed by the master account Use GuardDuty’s integration with Amazon SNS to report on findings
- C . Use Amazon Athena and Amazon QuickSight to build reports off of AWS CloudTrail Create a daily Amazon CloudWatch trigger to run the report dally and email It using Amazon SNS
- D . Use AWS Artifact’s prebuilt reports and subscriptions Subscribe the Director of Information Security to the reports by adding the Director as the security alternate contact tor each account
Two Amazon EC2 instances in different subnets should be able to connect to each other but cannot. It has been confirmed that other hosts in the same subnets are able to communicate successfully, and that security groups have valid ALLOW rules in place to permit this traffic.
Which of the following troubleshooting steps should be performed?
- A . Check inbound and outbound security groups, looking for DENY rules.
- B . Check inbound and outbound Network ACL rules, looking for DENY rules.
- C . Review the rejected packet reason codes in the VPC Flow Logs.
- D . Use AWS X-Ray to trace the end-to-end application flow
A company’s Security Officer is concerned about the risk of AWS account root user logins and has assigned a Security Engineer to implement a notification solution for near-real-time alerts upon account root user logins.
How should the Security Engineer meet these requirements?
- A . Create a cron job that runs a script lo download the AWS IAM security credentials We.
parse the file for account root user logins and email the Security team’s distribution 1st - B . Run AWS CloudTrail logs through Amazon CloudWatch Events to detect account roo4 user logins and trigger an AWS Lambda function to send an Amazon SNS notification to the Security team’s distribution list.
- C . Save AWS CloudTrail logs to an Amazon S3 bucket in the Security team’s account Process the CloudTrail logs with the Security Engineer’s logging solution for account root user logins Send an Amazon SNS notification to the Security team upon encountering the account root user login events
- D . Save VPC Plow Logs to an Amazon S3 bucket in the Security team’s account and process the VPC Flow Logs with their logging solutions for account root user logins Send an Amazon SNS notification to the Security team upon encountering the account root user login events
A company has multiple AWS accounts that are part of AW5 Organizations. The company’s Security team wants to ensure that even those Administrators with full access to the company’s AWS accounts are unable to access the company’s Amazon S3 buckets
How should this be accomplished?
- A . UseSCPs
- B . Add a permissions boundary to deny access to Amazon S3 and attach it to all roles
- C . Use an S3 bucket policy
- D . Create a VPC endpoint for Amazon S3 and deny statements for access to Amazon S3
A company uses HTTP Live Streaming (HLS) to stream live video content to paying subscribers by using Amazon CloudFront. HLS splits the video content into chunks so that the user can request the right chunk based on different conditions Because the video events last for several hours, the total video is made up of thousands of chunks
The origin URL is not disclosed and every user is forced to access the CloudFront URL The company has a web application that authenticates the paying users against an internal repository and a CloudFront key pair that is already issued.
What is the simplest and MOST effective way to protect the content?
- A . Develop the application to use the CloudFront key pair to create signed URLs that users will use to access the content.
- B . Develop the application to use the CloudFront key pair to set the signed cookies that users will use to access the content.
- C . Develop the application to issue a security token that Lambda@Edge will receive to authenticate and authorize access to the content
- D . Keep the CloudFront URL encrypted inside the application, and use AWS KMS to resolve the URL on-the-fly after the user is authenticated.
An organization policy states that all encryption keys must be automatically rotated every 12 months.
Which AWS Key Management Service (KMS) key type should be used to meet this requirement?
- A . AWS managed Customer Master Key (CMK)
- B . Customer managed CMK with AWS generated key material
- C . Customer managed CMK with imported key material
- D . AWS managed data key
A security engineer is responsible for providing secure access to AWS resources for thousands of developer in a company’s corporate identity provider (idp). The developers access a set of AWS services from the corporate premises using IAM credential. Due to the velum of require for provisioning new IAM users, it is taking a long time to grant access permissions. The security engineer receives reports that developer are sharing their IAM credentials with others to avoid provisioning delays. The causes concern about overall security for the security engineer.
Which actions will meet the program requirements that address security?
- A . Create an Amazon CloudWatch alarm for AWS CloudTrail Events Create a metric filter to send a notification when me same set of IAM credentials is used by multiple developer
- B . Create a federation between AWS and the existing corporate IdP Leverage IAM roles to provide federated access to AWS resources
- C . Create a VPN tunnel between the corporate premises and the VPC Allow permissions to all AWS services only if it originates from corporate premises.
- D . Create multiple IAM rotes for each IAM user Ensure that users who use the same IAM credentials cannot assume the same IAM role at the same time.
A company requires that SSH commands used to access its AWS instance be traceable to the user who executed each command.
How should a Security Engineer accomplish this?
- A . Allow inbound access on port 22 at the security group attached to the instance Use AWS Systems Manager Session Manager for shell access to Amazon EC2 instances with the user tag defined Enable Amazon CloudWatch togging tor Systems Manager sessions
- B . Use Amazon S3 to securely store one Privacy Enhanced Mail Certificate (PEM file) for each user Allow Amazon EC2 to read from Amazon S3 and import every user that wants to use SSH to access EC2 instances Allow inbound access on port 22 at the security group attached to the instance Install the Amazon CloudWatch agent on the EC2 instance and configure it to ingest audit logs for the instance
- C . Deny inbound access on port 22 at the security group attached to the instance Use AWS Systems Manager Session Manager tor shell access to Amazon EC2 instances with the user tag defined Enable Amazon CloudWatch togging for Systems Manager sessions
- D . Use Amazon S3 to securely store one Privacy Enhanced Mall Certificate (PEM fie) for each team or group Allow Amazon EC2 to read from Amazon S3 and import every user that wants to use SSH to access EC2 instances Allow inbound access on pod 22 at the security group attached to the instance Install the Amazon CloudWatch agent on the EC2 instance and configure it to ingest audit logs for the instance
A company’s information security team wants to analyze Amazon EC2 performance and utilization data in the near-real time for anomalies. A Sec Engineer is responsible for log aggregation. The Engineer must collect logs from all of the company’s AWS accounts in centralized location to perform the analysis.
How should the Security Engineer do this?
Log in to each account four te a day and filter the AWS CloudTrail log data, then copy and paste the logs in to the Amazon S3 bucket in the destination account.
- A . Set up Amazon CloudWatch to stream data to an Amazon S3 bucket in each source account. Set up bucket replication for each source account into a centralized bucket owned by the security Engineer.
- B . Set up an AWS Config aggregator to collect AWS configuration data from multiple sources.
- C . Set up an AWS config aggregator to collect AWS configuration data from multiple sources.
- D . Set up Amazon CloudWatch cross-account log data sharing with subscriptions in each account. Send the logs to Amazon Kinesis Data Firehose in the Security Engineer’s account.
A Security Engineer is setting up an AWS CloudTrail trail for all regions in an AWS account. For added security, the logs are stored using server-side encryption with AWS KMS-managed keys (SSE-KMS) and have log integrity validation enabled.
While testing the solution, the Security Engineer discovers that the digest files are readable, but the log files are not.
What is the MOST likely cause?
- A . The log files fail integrity validation and automatically are marked as unavailable.
- B . The KMS key policy does not grant the Security Engineer’s IAM user or role permissions to decrypt with it.
- C . The bucket is set up to use server-side encryption with Amazon S3-managed keys (SSE-S3) as the default and does not allow SSE-KMS-encrypted files.
- D . An IAM policy applicable to the Security Engineer’s IAM user or role denies access to the "CloudTrail/" prefix in the Amazon S3 bucket
A security engineer has created an Amazon Cognito user pool. The engineer needs to
manually verify the ID and access token sent by the application for troubleshooting purposes
What is the MOST secure way to accomplish this?
- A . Extract the subject (sub), audience (aud), and cognito:username from the ID token payload Manually check the subject and audience for the user name In the user pool
- B . Search for the public key with a key ID that matches the key ID In the header of the token. Then use a JSON Web Token (JWT) library to validate the signature of the token and extract values, such as the expiry date
- C . Verify that the token is not expired. Then use the token_use claim function In Amazon Cognito to validate the key IDs
- D . Copy the JSON Web Token (JWT) as a JSON document Obtain the public JSON Web Key (JWK) and convert It to a pem file. Then use the file to validate the original JWT.
A Security Engineer launches two Amazon EC2 instances in the same Amazon VPC but in separate Availability Zones. Each instance has a public IP address and is able to connect to external hosts on the internet. The two instances are able to communicate with each other by using their private IP addresses, but they are not able to communicate with each other when using their public IP addresses.
Which action should the Security Engineer take to allow communication over the public IP addresses?
- A . Associate the instances to the same security groups.
- B . Add 0.0.0.0/0 to the egress rules of the instance security groups.
- C . Add the instance IDs to the ingress rules of the instance security groups.
- D . Add the public IP addresses to the ingress rules of the instance security groups.
D
Explanation:
https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/security-group-rules-reference.html#sg-rules-other-instances
A company uses multiple AWS accounts managed with AWS Organizations Security engineers have created a standard set of security groups for all these accounts. The security policy requires that these security groups be used for all applications and delegates modification authority to the security team only.
A recent security audit found that the security groups are inconsistency implemented across accounts and that unauthorized changes have been made to the security groups. A security engineer needs to recommend a solution to improve consistency and to prevent unauthorized changes in the individual accounts in the future.
Which solution should the security engineer recommend?
- A . Use AWS Resource Access Manager to create shared resources for each requited security group and apply an IAM policy that permits read-only access to the security groups only.
- B . Create an AWS CloudFormation template that creates the required security groups Execute the template as part of configuring new accounts Enable Amazon Simple Notification Service (Amazon SNS) notifications when changes occur
- C . Use AWS Firewall Manager to create a security group policy, enable the policy feature to identify and revert local changes, and enable automatic remediation
- D . Use AWS Control Tower to edit the account factory template to enable the snare security groups option Apply an SCP to the OU or individual accounts that prohibits security group modifications from local account users
A company’s security information events management (SIEM) tool receives new AWS CloudTrail logs from an Amazon S3 bucket that is configured to send all object created event notification to an Amazon SNS topic An Amazon SQS queue is subscribed to this SNS topic. The company’s SEM tool then ports this SQS queue for new messages using an IAM role and fetches new log events from the S3 bucket based on the SQS messages. After a recent security review that resulted m restricted permissions, the SEM tool has stopped receiving new CloudTral logs
Which of the following are possible causes of this issue? (Select THREE)
- A . The SOS queue does not allow the SQS SendMessage action from the SNS topic
- B . The SNS topic does not allow the SNS Publish action from Amazon S3
- C . The SNS topic is not delivering raw messages to the SQS queue
- D . The S3 bucket policy does not allow CloudTrail to perform the PutObject action
- E . The IAM role used by the 5EM tool does not have permission to subscribe to the SNS topic
- F . The IAM role used by the SEM tool does not allow the SQS DeleteMessage action.
A city is implementing an election results reporting website that will use Amazon GoudFront The website runs on a fleet of Amazon EC2 instances behind an Application Load Balancer (ALB) in an Auto Scaling group. Election results are updated hourly and are stored as .pdf tiles in an Amazon S3 bucket. A Security Engineer needs to ensure that all external access to the website goes through CloudFront.
Which solution meets these requirements?
- A . Create an IAM role that allows CloudFront to access the specific S3 bucket. Modify the S3 bucket policy to allow only the new IAM role to access its contents. Create an interface VPC endpoint for CloudFront to securely communicate with the ALB.
- B . Create an IAM role that allows CloudFront to access the specific S3 bucket. Modify the S3 bucket policy to allow only the new IAM role to access its contents. Associate the ALB with a security group that allows only incoming traffic from the CloudFront service to communicate with the ALB.
- C . Create an origin access identity (OAI) in CloudFront. Modify the S3 bucket policy to allow only the new OAI to access the bucket contents. Create an interface VPC endpoint for CloudFront to securely communicate with the ALB.
- D . Create an origin access identity (OAI) in CloudFront. Modify the S3 bucket policy to allow only the new OAI to access the bucket contents. Associate the ALB with a security group that allows only incoming traffic from the CloudFront service to communicate with the ALB.
An company is using AWS Secrets Manager to store secrets that are encrypted using a CMK and are stored in the security account 111122223333. One of the company’s production accounts. 444455556666, must to retrieve the secret values from the security account 111122223333. A security engineer needs to apply a policy to the secret in the security account based on least privilege access so the production account can retrieve the secret value only.
Which policy should the security engineer apply?
- A . Option A
- B . Option B
- C . Option C
- D . Option D