Amazon SAA-C02 AWS Certified Solutions Architect – Associate Online Training
Amazon SAA-C02 Online Training
The questions for SAA-C02 were last updated at Feb 28,2026.
- Exam Code: SAA-C02
- Exam Name: AWS Certified Solutions Architect – Associate
- Certification Provider: Amazon
- Latest update: Feb 28,2026
A company is designing a new web service that will run on Amazon EC2 instances behind an Elastic Load Balancer. However many of the web service clients can only reach IP addresses whitelisted on their firewalls.
What should a solutions architect recommend to meet the clients’ needs?
- A . A Network Load Balancer with an associated Elastic IP address
- B . An Application Load Balancer with an associated Elastic IP address.
- C . An A record in an Amazon Route 53 hosted zone pointing to an Elastic IP address
- D . An EC2 instance with a public IP address running as a proxy in front of the load balancer.
A company needs to implement a relational database with a multi-Region disaster recovery Recovery Point Objective (RPO) of 1 second and an Recovery Time Objective (RTO) of 1 minute
Which AWS solution can achieve this?
- A . Amazon Aurora Global Database
- B . Amazon DynamoDB global tables
- C . Amazon RDS for MySQL with Multi-AZ enabled
- D . Amazon RDS for MySQL with a cross-Region snapshot copy
The following IAM policy is attached to an IAM group.
This is the only policy applied to the group.
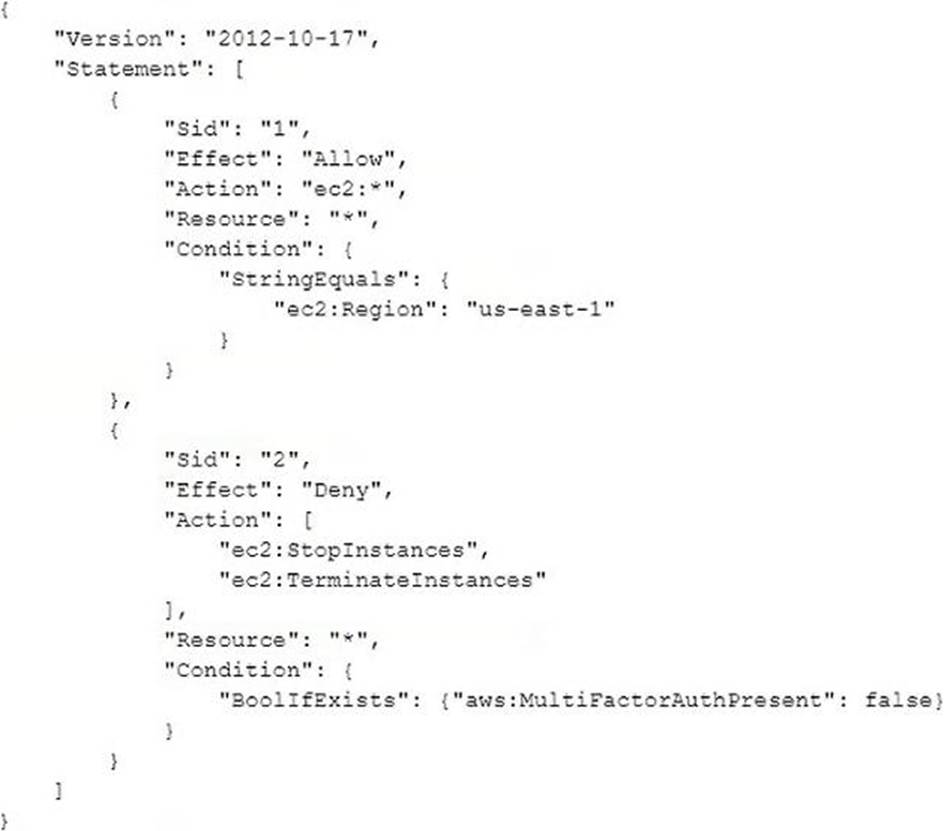
What are the effective IAM permissions of this policy for group members?
- A . Group members are permitted any Amazon EC2 action within the us-east-1 Region. Statements after the Allow permission are not applied.
- B . Group members are denied any Amazon EC2 permissions in the us-east-1 Region unless they are logged in with multi-factor authentication (MFA).
- C . Group members are allowed the ec2 Stoplnstances and ec2. TerminateInstances permissions for all Regions when logged in with multi-factor authentication (MFA) Group members are permitted any other Amazon EC2 action.
- D . Group members are allowed the ec2 Stoplnstances and ec2. Terminateinstances permissions for the us-east-1 Region only when logged in with multi-factor authentication (MFA) Group members are permitted any other Amazon EC2 action within the us-east-1 Region.
D
Explanation:
https://docs.aws.amazon.com/AWSEC2/latest/APIReference/ec2-api-permissions.html
By default, AWS Identity and Access Management (IAM) users don’t have permission to create or modify Amazon EC2 resources, or perform tasks using the Amazon EC2 API. To allow IAM users to create or modify resources and perform tasks, you must create IAM policies that grant IAM users permissions for the specific resources and API actions they’ll need to use, and then attach those policies to the IAM users or groups that require those permissions.
A company is running a highly sensitive application on Amazon EC2 backed by an Amazon RDS database Compliance regulations mandate that all personally identifiable information (Pll) be encrypted at rest.
Which solution should a solutions architect recommend to meet this requirement with the LEAST amount of changes to the infrastructure?
- A . Deploy AWS Certificate Manager to generate certificates Use the certificates to encrypt the database volume
- B . Deploy AWS CloudHSM, generate encryption keys, and use the customer master key (CMK) to encrypt database volumes
- C . Configure SSL encryption using AWS Key Management Service customer master keys (AWS KMS CMKs) to encrypt database volumes.
- D . Configure Amazon Elastic Block Store (Amazon EBS) encryption and Amazon RDS encryption with AWS Key Management Service (AWS KMS) keys to encrypt instance and database volumes
An ecommerce company hosts its analytics application in the AWS Cloud. The application generates about 300 MB of data each month. The data is stored in JSON format. The company is evaluating a disaster recovery solution to back up the data. The data must be accessible in milliseconds if it is needed, and the data must be kept for 30 days.
Which solution meets these requirements MOST cost-effectively?
- A . Amazon Elasticsearch Service (Amazon ES)
- B . Amazon S3 Glacier
- C . Amazon S3 Standard
- D . Amazon RDS for PostgreSQL
The application’s traffic is often low. but it occasionally grows significantly. During these sudden increases in traffic, DynamoDB returns throttling errors. The result is that error pages are displayed to end users.
What should a solutions architect do to reduce these errors?
- A . Change the DynamoDB table to use on-demand capacity mode.
- B . Create a DynamoDB read replica to scale the read traffic horizontally.
- C . Purchase DynamoDB reserved capacity of 1,000 RCUs and 500 WCUs.
- D . Configure the application to use strongly consistent reads for DynamoDB queries.
A solutions architect must design a highly available infrastructure for a website. The website is powered by Windows web servers that run on Amazon EC2 instances. The solutions architect must implement a solution that can mitigate a large-scale DDoS attack that originates from thousands of IP addresses. Downtime is not acceptable for the website.
Which actions should the solutions architect take to protect the website from such an attack? (Select TWO.)
- A . Use AWS Shield Advanced to stop the DDoS attack.
- B . Configure Amazon GuardDuty to automatically block the attackers.
- C . Configure the website to use Amazon CloudFront for both static and dynamic content.
- D . Use an AWS Lambda function to automatically add attacker IP addresses to VPC network ACLs.
- E . Use EC2 Spot Instances in an Auto Scaling group with a target tracking scaling policy that is set to 80% CPU utilization
A company runs an application on Amazon EC2 instances. The application is deployed in private subnets in three Availability Zones of the us-east-1 Region. The instances must be able to connect to the internet to download files. The company wants a design that is highly available across the Region.
Which solution should be implemented to ensure that there are no disruptions to internet connectivity?
- A . Deploy a NAT instance in a private subnet of each Availability Zone.
- B . Deploy a NAT gateway in a public subnet of each Availability Zone
- C . Deploy a transit gateway in a private subnet of each Availability Zone.
- D . Deploy an internet gateway in a public subnet of each Availability Zone
A bicycle sharing company is developing a multi-tier architecture to track the location of its bicycles during peak operating hours. The company wants to use these data points in its existing analytics platform A solutions architect must determine the most viable multi-tier option to support this architecture. The data points must be accessible from the REST API.
Which action meets these requirements for storing and retrieving location data?
- A . Use Amazon Athena with Amazon S3
- B . Use Amazon API Gateway with AWS Lambda
- C . Use Amazon QuickSight with Amazon Redshift.
- D . Use Amazon API Gateway with Amazon Kinesis Data Analytics
A development team needs to host a website that will be accessed by other teams. The website contents consist of HTML. CSS, client-side JavaScript, and images.
Which method is the MOST cost-effective for hosting the website?
- A . Containerize the website and host it in AWS Fargate.
- B . Create an Amazon S3 bucket and host the website there
- C . Deploy a web server on an Amazon EC2 instance to host the website.
- D . Configure an Application Loa d Balancer with an AWS Lambda target that uses the Express js framework.
Latest SAA-C02 Dumps Valid Version with 230 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

