At which stage of the Cyber-Attack Lifecycle would the attacker attach an infected PDF file to an email?
At which stage of the Cyber-Attack Lifecycle would the attacker attach an infected PDF file to an email?
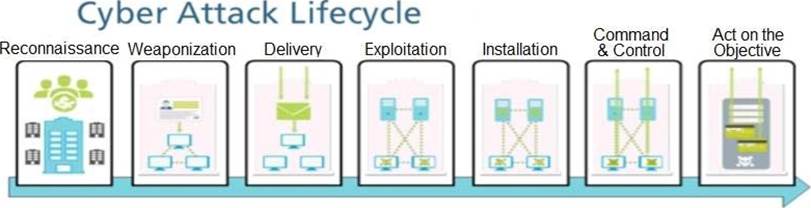
A . Delivery
B . Reconnaissance
C . Command and Control
D . Exploitation
Answer: D
Latest PCNSA Dumps Valid Version with 115 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments
Inline Feedbacks
View all comments

