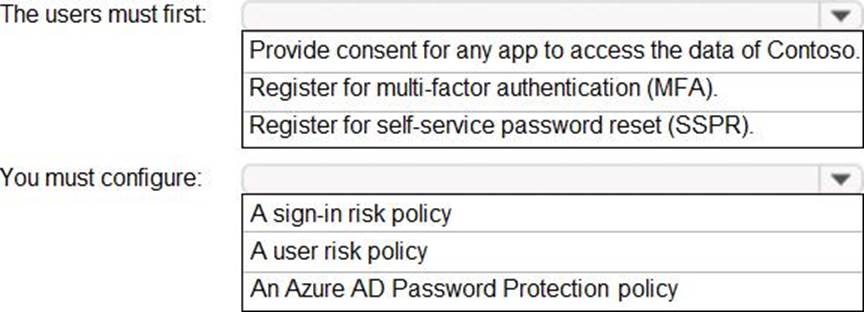
What should the users do first, and what should you configure?
HOTSPOT
You need to meet the technical requirements for the probability that user identities were compromised.
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Answer: 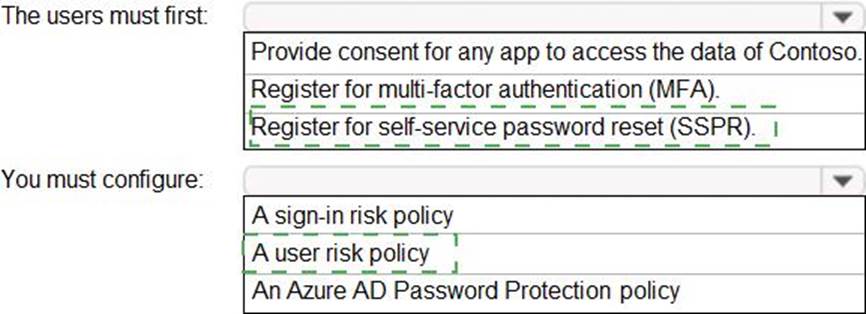
Latest SC-300 Dumps Valid Version with 106 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments

